Sichere Downloadquelle oder Malwareschleudern – Wie vertrauenswürdig sind Downloadportale noch?
Der Begriff „Download-Wrapper“ ist allgemein noch wenig bekannt, was leider nichts am Risikopotenzial der zugrunde liegenden Technologie ändert. Spätestens wenn einige Hacker und Malware-Autoren sich auf Download-Wrapper spezialisieren, dürfte die Internetgemeinschaft mit neuen Infektionswellen zu kämpfen haben. Erfahren Sie daher in diesem Artikel, wie Sie der potenziellen Gefahr aus dem Weg gehen – und wie diese überhaupt genau aussieht.
Wenn Sie bei dem Anglizismus „Download-Wrapper“ an eine gefüllte Teigrolle gedacht haben, liegen Sie gar nicht mal so falsch. Denn Wrapper sind allgemein Software, welche eine andere Software umgeben, so wie bei der Fastfood-Variante Teig die Füllung umgibt.
Download-Wrapper werden in letzter Zeit von immer mehr Download-Portalen eingesetzt, um die eigentliche Zieldatei herunter zu laden. Beim Versuch, ein Programm eines bestimmten Herstellers herunter zu laden, erhalten Sie also stattdessen zuerst einmal den Download-Wrapper. Dieser lädt dann wiederum das von Ihnen gewünschte Programm auf den Rechner. Während des Downloads zeigt Ihnen der Wrapper dann nervige Werbebanner oder jubelt Ihnen gar mit aggressiven Tricks andere Software oder Toolbars unter, die Sie gar nicht haben wollen.
Wozu Download-Wrapper?
Zu Recht darf nun gefragt werden, welchen Sinn Download-Wrapper erfüllen, denn immerhin sind konventionelle Downloads sowohl simpel als auch seit Jahrzehnten etabliert. Die Gründe sind vielfältig: Meist werden Komfortfunktionen wie das Pausieren und Fortsetzen großer Downloads beworben. Aktuelle Browser unterstützen diese Funktionen aber ebenso. Wahlweise könnte man auch eine professionelle Download-Manager Software einsetzen, statt sich den Wrapper aufzwingen zu lassen. Das Argument ist zudem schwammig, da die Download-Wrapper oft auch bei sehr kleinen Zieldateien zum Einsatz kommen, teilweise sogar bei kleineren als der Wrapper selbst.
Aus Sicht der Downloadportale sollte vor allem ein Argument für die Nutzung von Download-Wrappern sprechen: die Möglichkeit des gezielten Platzierens von Werbung. Eigens programmierte Software bietet dazu mehr Möglichkeiten als eine Webseite. Zusätzlich können statistische Daten beispielsweise zur verwendeten Hardware gesammelt werden, was detailliertere Benutzerprofile ermöglicht. Nicht ganz vergessen werden sollte auch der eigene Werbeeffekt: Wenn ich als Nutzer Software von einem bestimmten Portal installiert habe, so ist die Wahrscheinlichkeit hoch, dass ich mir den Namen merke und das Portal von nun an regelmäßig für Downloads verwende. Regelmäßige Besuche, am besten noch versehen mit eindeutigen Nutzerstatistiken, bedeuten wiederum mehr Werbeeinnahmen.
Aktuelle Beispiele und die Gefahren
Beispiel 1: download.com
Klicken Sie beim weltweit größten Download-Portal auf den Download-Button einer Datei, der mit dem kleinen Vermerk „CNET Installer enabled“ versehen ist, erhalten Sie statt der gewünschten Datei einen Wrapper, der etwa ein halbes Megabyte groß ist. Nach öffentlichen Protesten und Klagedrohungen von einigen Softwareherstellern verwendet das Portal den Wrapper mittlerweile nur noch für Programme, bei denen der jeweilige Hersteller keinen Widerspruch eingelegt hat (oder womöglich noch gar nichts davon weiß, dass seine Software ‚verpackt‘ wurde).
Risiko: Installation einer Browser-Toolbar und Manipulation der Startseite.
Vorsicht! Lassen Sie sich nur nicht dazu hinreißen, immer auf „Next Step“ zu klicken. Sie würden die in der rechten unteren Ecke versteckte Option „I do not accept“ übersehen, über die man die Installation der zusätzlichen Toolbar abwählen kann.
Bilderstrecke: Ablauf des CNET Download.com Installers
Beispiel 2: softonic.com
Auch beim mehrsprachigen Portal „Softonic“ ist es mittlerweile gang und gäbe, dass man statt dem gewünschten Download zuerst einmal einen Wrapper erhält. Dieser ist mit etwas mehr als 300 KB zwar einer der kleinsten, zeigt dafür aber die aggressivste Werbung. Hinter dem Abschnitt „Options“ verbirgt sich lediglich eine Werbeseite für ein aus einem Pool ausgewähltes Programm eines Drittherstellers. Auch hier ist die Installation vorausgewählt. Wählt man diese ab, erscheint sogleich eine zweite Werbeseite für ein anderes Programm. Startet der Download dann endlich, wird nochmal ein Werbebanner für ein drittes Programm angezeigt, der auch nach dem Ende des Downloads noch einmal in den Vordergrund gerückt wird. Mit dieser Werbe-Penetration toppt Softonic definitiv alle uns bekannten Wrapper.
Risiko: Installation einer unerwünschten Software, irreführende Werbebanner.
Bilderstrecke: Ablauf des Softonic Download Wrappers
Beispiel 3: softonic.de / RegNow
Die deutsche Version von Softonic wirbt bei dem von uns getesteten Download mit einem direkten Hersteller-Downloadlink. Dieser führt aber nicht wie erwartet auf die Installationsdatei, sondern geradewegs zu einem anderen Wrapper, jenem vom des Zahlungsdienstleisters RegNow. Der Wrapper ist mit rund 300 KB ebenfalls relativ klein, zeigt jedoch beim Start umgehend ein Spezialangebot für eine Dritthersteller-Software. Ein Klick auf den fälschlicherweise als „Options“ bezeichneten Button offenbart, dass RegNow den Wrapper nicht einmal selbst gebaut hat, sondern wiederum einem externen Entwickler namens GetRightToGo.com vertraut.
Risiko: Unbewusste Umleitung auf unbekannte Dienstleister, Werbebanner.
Bilderstrecke: Ablauf des RegNow Download Wrappers
Beispiel 4: tucows.com
Der Veteran unter den Downloadportalen geht unserer Meinung nach am hinterhältigsten von allen vor: Der Wrapper namens „AVG CloudInstaller“ lässt erst einmal nur die Wahl zwischen „Express“- und „Custom“-Installation der AVG Toolbar. Ein Überspringen ist nur dadurch möglich, dass man unten auf den „Decline“-Button klickt. Dieser suggeriert jedoch auf den ersten Blick, dass man damit den Download bzw. die Installation des eigentlich gewünschten Programms abbricht. Egal ob Express oder Custom, die Standardvorgabe ist in beiden Fällen, dass die Browser-Startseite sowie der Standard-Suchanbieter manipuliert werden, sowie eine Toolbar installiert wird.
Risiko: Größte Gefährdung für unbeabsichtigte Installation fremder Software sowie Manipulationen des Browsers.
Hinweis: Die dem Wrapper zugrunde liegende Technologie der Firma „OpenInstall Inc.“ wird nebst Signaturen-Scan auch von der Emsisoft Verhaltensanalyse als potenziell gefährlich gemeldet, da sie nach dem Download und der Beendigung noch einmal Daten unsichtbar ins Internet schickt. Vermutlich zu Statistik-Zwecken.
Bilderstrecke: Ablauf des Tucows Download Wrappers
Werbeeinnahmen mit aller Gewalt
Die Absicht einer Download-Plattform sich per Werbung zu finanzieren ist nachvollziehbar, immerhin kostet Traffic Geld. Allerdings stellen diese Download-Wrapper ein enormes Sicherheitsrisiko dar. An erster Stelle wird der Nutzer in seiner Absicht ein bestimmtes Programm zu downloaden getäuscht: Er erhält nämlich erst einmal nicht das Zielprogramm, sondern eben den Wrapper. Gerade nicht Internet-affine Anwender kann dieser Vorgang leicht verwirren.
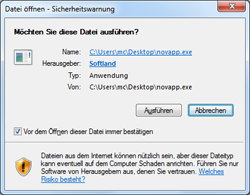
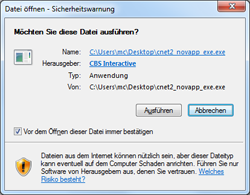
Schlimmer noch aus unserer Sicht ist, dass der Anwender die Code-Signatur des Herstellers bei der Ausführung der heruntergeladenen Datei nicht mehr sieht. Dies öffnet Hackern potenziell Tür und Tor, denn sie müssen nur noch das Download-System infiltrieren und können dann beliebig eigene Software verteilen. Denn Sie als Nutzer sehen ja nicht mehr, was genau Sie dort herunterladen, das gewünschte Tool oder etwa einen Trojaner – oder beides.
ORIGINAL – WRAPPER
Zudem reicht einmal mehr auch hier ein unsauber programmierter Wrapper, dessen Schwachstellen theoretisch ausgenutzt werden können, um die Kontrolle über Ihren Computer zu erlangen. Prinzipiell stellt jedes installierte und vor allem ausgeführte Programm eine Gefahr dar – Grund genug, auf eigentlich unnötige Software wie Wrapper zu verzichten. Die Möglichkeit der Erstellung von Nutzerprofilen und der Installation weiterer Software wie beispielsweise einer Toolbar anhand des Download-Wrappers sei an dieser Stelle auch nochmal als klarer Negativpunkt erwähnt.
Unsere Empfehlung: Meiden Sie Portale, die Wrapper verwenden
Aufgrund der fehlenden technischen Notwendigkeit für Download-Wrapper und dem mit ihnen verbundenen Gefahrenpotenzial empfehlen wir schlicht und einfach Webseiten, die diese Technologie einsetzen, zu meiden.
Achten Sie beim Download einer Datei auf den Dateinamen – er sollte im Normalfall keinen Hinweis auf einen Wrapper im Dateinamen enthalten und die Datei sollte annähernd die in der Beschreibung angegebene Größe aufweisen. Emsisoft Anti-Malware laden Sie beispielsweise als EmsisoftAntiMalwareSetup.exe von unserem Server, genauso heißt die Setup-Datei auch bei chip.de oder computerbild.de. Bei Softonic deutet der Dateiname SoftonicDownloader_fuer_emsisoft-emergency-kit.exe klar darauf hin, dass zunächst der Softonic eigene Downloader auf dem PC landet. Bei anderen Portalen ist die Art der Namensgebung ähnlich, wie z.B. eines der folgenden Kürzel am Anfang des Dateinamens:
- cnet2_<name>
- Download_<name>
- SoftonicDownloader_for_<name>
- oi_<name>
Leicht erkennbar sind die Download-Wrapper auch über ihr Dateisymbol, da sie immer das gleiche verwenden:
Verschiedene Symbole der Wrapper
Abhilfe
Sollte sich ein Download-Wrapper in bereits installierter Form auf Ihrem PC befinden, so empfiehlt sich eine simple Deinstallation. Auch die meisten mitinstallierten Toolbars und Gratis-Addons lassen sich so deinstallieren. Eine Übersicht aller auf Ihrem PC installierter Programme finden Sie über den Punkt „Programme“ in der Windows 7 oder Vista Systemsteuerung, bei Windows XP unter „Software“. Veränderte Einstellungen wie die Browser-Startseite oder der Standard-Suchanbieter müssen jedoch von Hand zurückgesetzt werden.
Emsisoft Anti-Malware meldet solche fragwürdigen Download-Wrapper als Riskware. Der Verhaltensanalyse-Wächter zeigt außerdem sofort einen Spyware-Alarm, wenn ein Wrapper unsichtbar im Hintergrund Daten vom Hersteller lädt oder welche an ihn überträgt.
Emsisoft Anti-Malware Alarm
Eine Malware freie Zeit wünscht
Ihr Emsisoft Team