Gefahren im Netzwerk: So nutzen Sie WLAN daheim und unterwegs sicher und effizient
![]()
Die Nutzung von WLAN ist dank dem damit verbundenen Komfort inzwischen zum Standard geworden. Im Garten sitzend im Internet surfen, unterwegs E-Mails abrufen oder im Hotel die noch unbekannte Stadt per Google Maps erkunden. All das war vor noch gar nicht langer Zeit schwierig bis unmöglich. Doch mit der kabellosen Netzanbindung wird oft sorglos umgegangen, so dass Hacker in vielen Fällen leichtes Spiel haben.
Wussten Sie beispielsweise, dass es in vielen Netzwerken und beim Besuch etlicher Webseiten möglich ist, Ihre gesendeten Daten mitzulesen? Doch nicht nur in fremden WLANs lauern Gefahren, auch Ihr eigenes Funknetzwerk bedarf des korrekten Schutzes. Eine unzureichende Verschlüsselung führt beispielsweise schnell dazu, dass Ihr Internetzugang zum Ausspionieren Ihrer Daten und für weitere illegale Aktivitäten missbraucht wird. Natürlich müssen Sie nicht auf den bequemen Internet-Lebensstandard verzichten, denn wir zeigen Ihnen, wie Sie die größten Risiken vermeiden und sowohl öffentliche Hotspots (Zugangspunkte), als auch das eigene WLAN sicher nutzen können.
Sichern Sie Ihr Heimnetzwerk vor unerwünschten Eindringlingen
Der WLAN-Empfang des Routers reicht in der Regel weiter als die eigenen vier Wände. Das ist zwar prinzipiell jedem klar, dennoch aber in gewisser Weise auch so abstrakt, dass es gerne vergessen wird. In ein offenes oder nur unzureichend gesichertes WLAN kann also jemand von außen leicht eindringen. Damit kann nicht nur Ihr erzeugter Internet-Traffic mit einem sogenannten „Sniffer“ abgehört werden – darunter Login-Daten für Foren, Webshops oder gar Online-Banking. Auch könnte Ihr Anschluss an das World Wide Web für Straftaten benutzt werden, beispielsweise In Form illegaler Downloads, dem Versand von Spam oder gar Angriffen auf Webportale. Durch die einmalige IP-Adresse ist Ihre Anbindung nachverfolgbar und ein potenzielles Strafverfahren die äußerst unangenehme Konsequenz.
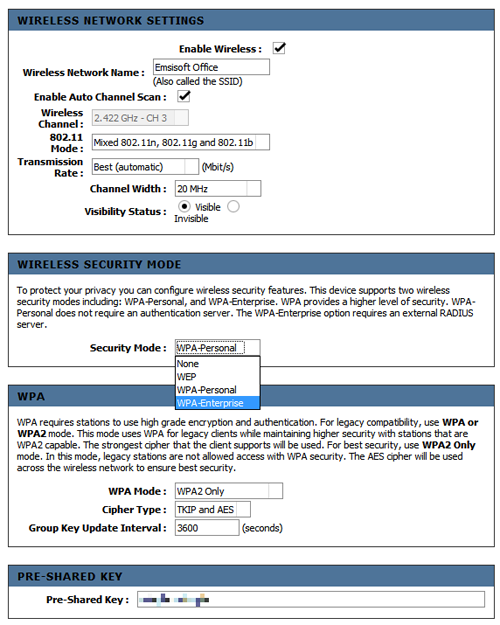
Es gilt also, Fremde aus dem eigenen Netzwerk fern zu halten. Der notwendige Schritt hierzu ist, eine gute Verschlüsselung zu verwenden. Das noch bis vor wenigen Jahren standardmäßig in Routern aktivierte Verschlüsselungsverfahren WEP ist längst nicht mehr zeitgemäß, WPA oder noch besser WPA2 mit einem ausreichend langen Passwort MUSS heute verwendet werden. WPA steht für „Wi-Fi Protected Access“ und ist ein allgemeiner Sicherheitsstandard für Funknetzwerke, welcher den überaus sicheren Advanced Encryption Standard (AES) verwendet. Da gegen dieses Verfahren eigentlich nur Wörterbuch-Attacken sinnvoll durchgeführt werden können, sollte das Passwort aus mindestens 15-20 Zeichen bestehen (neben Buchstaben auch Zahlen und idealerweise Sonderzeichen), damit es nach aktuellen Maßstäben als ausreichend schwer knackbar gilt. Wie genau Sie WPA2 bei Ihrem Router aktivieren, entnehmen Sie bitte gegebenenfalls dem Handbuch des Geräts.
Brisantes Detail: Gerichtsurteile in den vergangenen Jahren haben gezeigt, dass die Verwendung von nicht mehr zeitgemäßer Verschlüsselung wie WEP rechtlich genauso gehandhabt wird wie gar keine Verschlüsselung. Mehrere Betreiber von Hotspots wurden wegen illegalen Datentransfers Dritter rechtmäßig verurteilt.
Einstellung der WLAN-Verschlüsselung bei einem modernen Router. WPA2 mit einem möglichst langen Passwort schützt Ihr Netzwerk vor ungebetenen Gästen.
Apropos Router: In der Regel ist auch dieser mit einem eigenen Passwort geschützt. Vermeiden Sie hier auf jeden Fall die Nutzung der Werkseinstellungen, sondern setzen Sie wiederum ein eigenes und möglichst langes Passwort. Die Router-Konfiguration ist zwar bei neueren Geräten nicht von außen erreichbar (nur über ein lokal eingestecktes Kabel), aber so besteht auf jeden Fall eine weitere Hürde. Auch sollten Sie die Firmware (Betriebssystem) des Routers stets aktuell halten, um möglicherweise neu entdeckte Lücken zu schließen. Gerade hier gab es in den letzten Jahren einige prominente Fälle bei namhaften Router-Herstellern.
Wer ganz auf Nummer sicher gehen will, deaktiviert zusätzlich noch das automatische Senden der SSID, also des Namens des WLAN Netzwerks. Im oberen Screenshot wäre das durch die Auswahl der Option „Invisible“ (Englisch für „unsichtbar“) möglich. Dies erschwert allerdings die Einrichtung des Zugangs auf diversen Geräten, da alle Daten manuell angegeben werden müssen. Diese Möglichkeit ist rein optional, für Ihr sicheres WLAN zuhause reicht eine WPA2 Verschlüsselung mit einem soliden Passwort sowie ein aktuell gehaltener Router prinzipiell aus.
Nicht ganz vernachlässigen sollte man allerdings den sozialen Faktor. Haben Sie beispielsweise öfters Besucher, die Sie nur entfernt kennen, aber kurz Ihr WLAN nutzen möchten? Egal ob Bekannte Ihrer Kinder, Couchsurfing-Gäste oder sonstiges, hier ist ein regelmäßiges Ändern des WPA Passwortes sinnvoll.
WLAN auch unterwegs richtig nutzen

Der Siegeszug von WLAN erstreckt sich nicht nur auf die eigene Wohnung. Längst hat das drahtlose Netzwerk auch unser auswärtiges Leben erobert. Sei es im Hotel, Restaurant oder der öffentliche Hotspot im Park, fast überall sind WLAN Zugänge Standard geworden. Viele fühlen sich zumindest in passwortgesicherten Netzwerken sicher, doch das ist ein fataler Trugschluss.
Denn Sie sind selten alleine im Netzwerk. Meist haben auch andere Nutzer die Zugangsdaten erhalten und teilen das WLAN mit Ihnen. Wenn Sie nun ungesicherte Webseiten ansteuern, können wiederum alle gesendeten Daten ausgeschnüffelt werden. Es besteht ergo dieselbe Gefahr, wie wenn Sie Ihr Heimnetzwerk gar nicht verschlüsseln, sondern offen betreiben würden. Nachrichten im Messenger, E-Mails oder gar Benutzerkonten können normal gesendet ausgelesen werden. Dazu müssen Ihre Mitsurfer nicht mal findige Hacker sein, es reichen ganz normale Sniffer-Tools, die im Internet heruntergeladen werden können.
Wir stellen fest: Die Verschlüsselung des Netzwerks an sich führt nicht dazu, dass die Daten innerhalb des Netzwerkes auch verschlüsselt werden, sondern regelt nur den Zugriff auf das Netzwerk selber. Sie können sich das so vorstellen, wie den Hauptschlüssel für ein Hochhaus. Alle Mieter können die gemeinsame Eingangstür unten öffnen, so wie Sie sich mit Zugangsdaten bei einem WLAN-Hotspot anmelden. Aber genauso wie jeder Mieter noch über einen einmaligen Schlüssel verfügt, um die eigentliche Wohnung zu betreten, müssen Sie auch die Übertragung Ihrer Daten sichern.
Dies geschieht über eine eigene Verschlüsselung, die unter der Abkürzung TLS bzw. SSL bekannt ist. TLS steht für „Transport Layer Security“ und ist die Nachfolgebezeichnung von SSL (Secure Sockets Layer). Das klingt kompliziert, ist aber prinzipiell nur die Bezeichnung für einen sicheren Datentransport. Jeder gängige Browser „versteht“ TLS bzw. SSL, wodurch Sie leicht und bequem Webseiten sicher ansteuern können. Problematischer ist hingegen die Seite der Webpräsenzen, denn selbst wenn der Browser TLS/SSL unterstützt, so muss dieser Service logischerweise auch von der gewünschten Internetseite angeboten werden. In der Realität ist das leider nicht immer der Fall.
Wenn Sie eine Webseite ansurfen, auf der Sie persönliche Daten eingeben, wie beispielsweise Facebook, ein Online-Kaufhaus oder Ihre Online-Banking Plattform, so sollte dies IMMER über HTTPS geschehen. Das steht für „HyperText Transfer Protocol Secure“, also eine sichere „http://“ Verbindung, welche auf TLS/SSL basiert (https://). Wenn die aufgerufene Webseite dies nicht unterstützt, sollten Sie die Eingabe persönlicher Daten tunlichst unterlassen.
Warum sind nicht alle Webseiten via HTTPS verfügbar?
Bevor Sie jetzt loslegen und die Betreiber sämtliche unverschlüsselter Webseiten kontaktieren, sei erwähnt, dass zum reinen Informationsabruf keine Verschlüsselung notwendig ist. Eine TLS/SSL-Bereitstellung ist wesentlich komplexer und aufwendiger im Betrieb für Webserver als simples unverschlüsseltes HTTP. Darüber hinaus hätte eine flächendeckende Verwendung von Verschlüsselung negative Auswirkungen auf die Internet-Infrastruktur, da z.B. von Providern gerne verwendetes Daten-Caching (Zwischenspeicherung) erschwert wird und die global übertragenen Datenmengen massiv steigen würden.
Das Emsisoft Lizenz-Center wird hier verschlüsselt über den Internet Explorer aufgerufen, erkennbar an dem https und dem Symbol rechts neben der Lupe.
So erkennen Sie korrekt gesicherte Webseiten
In den gängigen Browsern erkennen Sie die Verwendung einer sicheren Verbindung neben dem https:// vor der URL auch an einem Symbol, wie beispielsweise einem kleinen Schloss beim Internet Explorer. Neben diesem muss peinlichst genau darauf geachtet werden, dass die Webseite über ein nicht gehacktes und gültiges Zertifikat verfügt. Glücklicherweise übernimmt die Überprüfung des Zertifikats der Browser für Sie, im Falle einer Warnmeldung oder eines ungültigen Zertifikats sollten Sie aber trotz „https“ in der Adresszeile oder Verschlüsselungssymbol von der Übertragung sensibler Daten absehen.
Ist hingegen alles korrekt, können Sie relativ bedenkenlos surfen. Für die Nutzung des World Wide Web außerhalb des Browsers wie etwa in Form eines E-Mail-Programms steht TLS/SSL ebenfalls zur Verfügung. Leider ist die Verwendung von TLS/SSL für den Austausch virtueller Post in der Realität nicht immer ganz so einfach. Zwar unterstützen viele E-Mail Dienstleister TLS oder SSL und es kann in den Einstellungen eigentlich jedes E-Mail Clients aktivieret werden, doch einige Internet-Provider machen einen Strich durch die sichere Rechnung, indem Sie die häufig verschlüsselte POP3- und SMTP-Zugänge blockieren. Unter diesen Umständen ist sicheres mailen nur durch einen https codierten Webmailer, einem alternativ angebotenen Port vom Mailserver oder die Nutzung eines VPN möglich.
Weitere Sicherheitsmaßnahmen bei WLAN-Nutzung
Eine sinnvolle Ergänzung beim Surfen in fremden WLAN-Netzen per Notebook stellt eine Firewall dar. Denn auch wenn Sie alle wichtigen Daten verschlüsselt übertragen, so ist Ihr Computer dennoch innerhalb des Netzwerks erreichbar. Über offene Ports oder Schwachstellen in Programmen können Angreifer unter Umständen die Kontrolle über Ihr Betriebssystem erhalten. Noch wichtiger ist allerdings, dass Sie keine ungesicherten Dateifreigaben erteilt haben. Denn auf zugänglich gemachte Dateien oder Drucker haben selbstverständlich wieder alle Nutzer desselben Hotspots Zugriff, falls diese nicht ebenfalls per Passwort gesichert sind.

Auch unterwegs haben Sie die Möglichkeit, sicherheitstechnisch noch einen Schritt weiter zu gehen. Das Zauberwort heißt hier VPN: Virtual Private Network, also virtuelles privates Netzwerk. Dazu wird eine eigene Software wie zum Beispiel das Windows-eigene PPTP oder das kostenfrei erhältliche OpenVPN benötigt. Sie verbinden sich nach der Installation wie sonst auch mit dem drahtlosen Netzwerk, der VPN-Client baut aber zwischen Ihrem Rechner und einem ständig im Internet befindlichen VPN-Server eine sichere Verbindung auf. Diese sichere Verbindung funktioniert nun wie ein Tunnel, durch den Sie Ihre Daten fast gefahrlos übertragen können.
Das Wort „fast“ steht nicht zufällig im letzten Satz, denn Computersicherheit hat die unangenehme Eigenschaft, dass es immer Schwachstellen gibt. Selbstverständlich muss der VPN-Server, zu dem Sie sich verbinden, sicher und vertrauenswürdig sein. Sicher heißt hierbei, dass nicht etwa der Datenverkehr direkt hinter dem Server abgehört werden kann oder der Betreiber gar selber illegales im Schilde führt. Seien Sie bei der Wahl Ihres VPN Anbieters also wachsam und vorsichtig.
Eine Malware freie Zeit wünscht
Ihr Emsisoft Team