Effektiver Schutz vor neuer Malware: Die Emsisoft Verhaltensanalyse
Was genau ist Verhaltensanalyse und wie funktioniert sie?
Der Emsisoft Anti-Malware Dateiwächter überprüft, genauso wie jeder andere Antiviren-Wächter, alle gestarteten Programme per Signaturen-Scan. Auch wenn hier ein besonders leistungsstarker Dual-Engine-Scanner zum Einsatz kommt, so kann neue Malware dennoch nur dann erkannt werden, wenn bereits eine Signatur für die Datei vorhanden ist. Eine Signatur ist vergleichbar mit einem Fingerabdruck, welcher bedingt, dass ein Straftäter – oder in unserem Fall das Schadprogramm – schon bekannt ist.
Zwischen dem ersten Auftreten neuer Malware und dem Update der Signaturen vergeht also immer wertvolle Zeit, in der der Computer ungeschützt ist. Genau aus diesem Grund entwickeln wir bereits seit 2005 die Emsisoft Verhaltensanalyse. Dabei handelt es sich um eine Technologie, die komplett ohne Signaturen gefährliche Malware erkennen und blockieren kann.
Jeder Malware-Typ, egal ob Virus, Trojaner, Keylogger, Rootkit oder Spyware, arbeitet immer nach einem bestimmten Schema. Jeder Typ hat in seinen Eigenschaften Haupt-Ziele, die ihn eindeutig unterscheidbar machen. Ein Virus infiziert, ein Wurm verbreitet sich, ein Keylogger zeichnet Tastatureingaben auf, ein Backdoor-Trojaner verschickt Daten, und so weiter. Ein Beispiel: Trojaner unterscheiden sich immer nur in der Weise, WIE sie Daten verschicken. Das täuscht jedoch nicht darüber hinweg, dass sie alle zusammen eben Daten verschicken.
Genau hier setzt die Emsisoft Verhaltensanalyse an. Sie analysiert das Verhalten aller aktiven Programme in Echtzeit und schlägt Alarm, sobald ein Programm ein gefährliches Verhalten zeigt. Um beim Straftäter-Beispiel zu bleiben: Stellen Sie sich vor, Ihnen begegnet Nachts auf der Straße eine suspekte Person. Anhand verschiedener Kriterien wie nervösem Umschauen, zielstrebigem Gang auf Sie zu oder gar dem Griff nach einer vermeintlichen Waffe, werden Sie zu einem bestimmten Zeitpunkt entscheiden, dass die Situation gefährlich werden könnte. Nach diesem Prinzip bewertet auch die Emsisoft Verhaltensanalyse alle Aktionen von aktiven Programmen, vor allem von Unsichtbaren im Hintergrund, die sie sonst nicht ohne weiteres wahrnehmen würden.
Wenn Sie jetzt denken, das klingt zu gut um wahr zu sein, liegen Sie richtig. Diese Technologie hat auch einen Nachteil. Verhaltensanalyse erkennt Malware am Verhalten, das Verhalten ist innerhalb eines Malware-Typs jedoch immer das gleiche. Daher kann die Verhaltensanalyse zwei unterschiedliche Schaddateien gleichen Typs nicht namentlich voneinander unterscheiden. Die Verhaltensanalyse kann Ihnen nicht sagen, ob der Wurm nun NetSky oder Bagle, oder ob der Trojaner Optix oder SubSeven heißt. Sie kann lediglich sagen, dass es sich um einen Wurm bzw. um einen Trojaner handelt. Das ist jedoch ein sehr geringer Preis, den man in Kauf nimmt, um diesen sehr mächtigen Schutz in Anspruch zu nehmen.
Was erkennt die Emsisoft Verhaltensanalyse?
Derzeit ist die Verhaltensanalyse für folgende Malware-Typen trainiert:
- Backdoor Trojaner (Hintertüren)
- Spyware/Adware
- HiJacker
- Würmer
- Dialer
- Keylogger/Banking Passwort Sniffer
- Trojan-Downloader
- Viren
- Rootkits
Es ist außerdem in der Lage, folgende potenziell gefährliche Aktionen anzuzeigen und zu unterbrechen:
- Installation von unbekannten Treibern und Diensten
- Jede Art von Prozess-Manipulation wie DLL-Injektion, Code-Injektion, Patchen, Terminieren, etc.
- Installation von neuen BHOs (Browser Helper Objects) und Toolbars
- Änderungen an den Browser Einstellungen
- Unsichtbare Installationen von Software
- Änderungen an der Hosts Datei (Umleitung von Webseiten)
- Installationen von Debuggern im System
- Erstellung neuer Autostart Einträge
- Simulierte Maus- und Keyboard-Aktivitäten
- Direkten Zugriff auf Sektoren der Festplatte
- Änderungen der System-Sicherheitsrichtlinien
Wie verhalte ich mich bei einer Alarm-Meldung?
Die Emsisoft Verhaltensanalyse ist ein System, das dazu entwickelt wurde, verdächtige Verhaltensweisen zu erkennen. Da sich das Verhalten von normalen Programmen und Malware teilweise überschneidet, kann es sich natürlich auch einmal irren. Daher sollten Sie zuerst alle Anzeichen in Betracht ziehen, bevor ein Programm vorschnell blockiert wird. Im Zweifelsfall können Sie eine verdächtige Datei auch jederzeit zur Analyse an uns übermitteln.
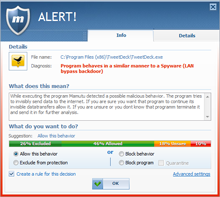
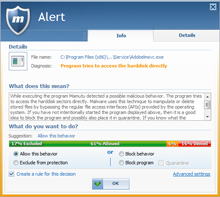
Prinzipiell kommen Fehlalarme mittlerweile aber sehr selten vor. Denn einerseits arbeitet die Emsisoft Verhaltensanalyse dank jahrelangem Finetuning äußerst effizient und andererseits können Sie dank der Community basierten Alarm-Reduktion die Intelligenz der Masse nutzen. Diese Funktion gibt bei Alarmmeldungen eine Empfehlung basierend auf den Entscheidungen aller anderen Nutzer ab: Eine übersichtliche Grafik illustriert, wie viel Prozent der Anwender welche Aktion ausgeführt haben (siehe Abbildung). Auf diese Weise können Sie schnell entscheiden, ob Sie das Verhalten des gemeldeten Programms erlauben (andere Verhaltensweisen werden weiterhin gemeldet), von der Beobachtung ausnehmen (volles Vertrauen), blockieren (Prozess wird beendet) oder in Quarantäne geben wollen (Prozess wird beendet und die exe Datei in Quarantäne verschoben damit sie nicht mehr gestartet werden kann).
Zusätzlich können Sie definieren, dass Anwendungen mit einem bestimmten Prozentwert automatisch erlaubt werden. Ein flüssiges Arbeiten ohne störende Popups ist damit gewährleistet und Ihnen wird die teils schwierige Entscheidungsfindung bei unbekannteren Prozessen abgenommen. Die Übermittlung der eigenen Entscheidungen an das Emsisoft Anti-Malware Network ist natürlich freiwillig und kann jederzeit deaktiviert werden.
Ein allgemeiner Tipp zur Nutzung der Verhaltensanalyse:
Nachdem Sie die Software installiert haben, stellen Sie bitte sicher, dass der Wächter aktiv ist und starten Sie dann Ihre meistgenutzten Programme, um mögliche Fehlalarme gleich vorab abzufangen. Dieser Vorgang dauert wenige Minuten und die Emsisoft Verhaltensanalyse ist auf Ihren PC optimal eingestellt.
Es ist übrigens ein Irrtum, dass es sich bei der Emsisoft Verhaltensanalyse um eine herkömmliche Heuristik handelt. Heuristiken untersuchen die Dateien auf der Festplatte auf schädliche Routinen hin und werten eine Datei als gefährlich oder sicher basierend auf einer Wahrscheinlichkeitsrechnung. Die Verhaltensanalyse arbeitet aber eine Ebene darüber und überwacht direkt das Verhalten der aktiven Programme im System.
Wohin kann ich mich bei Fragen wenden?
Sollten Sie nicht sicher sein, ob ein bestimmtes Programm wirklich gefährlich ist, hilft Ihnen unser Support-Team gerne weiter. Sie können uns über das Support Forum oder per E-Mail jederzeit kontaktieren und erhalten schnell Antworten von unseren Sicherheitsspezialisten.
Eine Malware freie Zeit wünscht
Ihr Emsisoft Team