Has the antivirus industry gone mad?


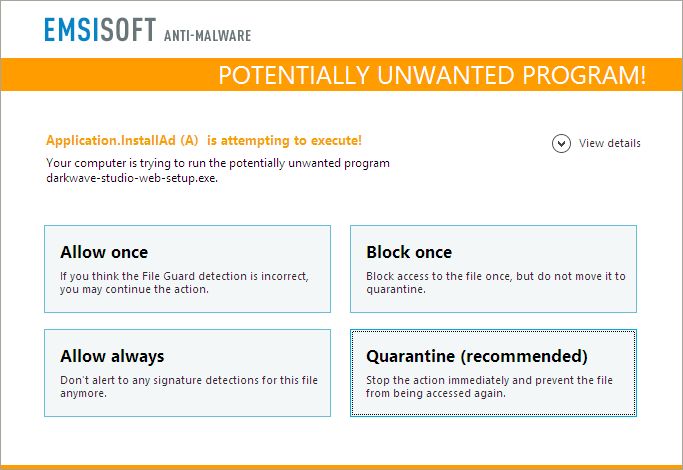
We have seen a concerning trend that is about to spiral out of control: Potentially Unwanted Programs (PUPs) are further on the rise. What’s even more concerning is how they are spreading. After big vendors as Oracle (Java) and Microsoft (Bing and Skype) started bundling, now antivirus vendors have joined the game. We did research on some of the most popular PUP practices among the freeware antivirus vendors, and the results are quite disturbing.
PUPs want to get on your computer to make money off of you
First, lets quickly recap what PUPs are and why they’re spreading like wildfire. PUPs are programs in the form of toolbars, adware, plugins or other downloads that sneak onto your computer. PUPs are not classified as malware (yet?), since they’re not always harmful but pretty much always annoying, hence the name “potentially” unwanted. But, PUPs are getting more and more unwanted than ever: just the fact that you don’t know what you’re installing is undesired. If you notice a sudden change in your computer’s speed, notice your search engine changed, experience annoying pop-up ads, notice new toolbars in your browser menu bar or any other sudden change in your computer’s behavior or layout, chances are high that your computer has one or more PUPs installed.
PUPs come in many shapes and forms, but they all have a few things in common:
- PUPs want to make money off of you. PUPs want to be on your computer for a reason, to make money off of you. The most common form is by hijacking your browser: they can then show you ads, monetize or sell your search and/or browser behavior or redirect your homepage.
- PUPs use aggressive distribution methods to get on your computer: we specifically used the word “sneak” onto your computer, because in the large majority of the cases, the user is not aware that he/she is installing a PUP.
- Most PUPs don’t have any significant value or advantages, so PUP producers have to get around this by paying other software vendors or distributors such as download portals $$$ per new installation that they get them.
- PUPs are often brought to you by freeware vendors: they frequently get on your computer bundled with a freeware program. While you’re installing program A, you also install one or more PUPs, often without knowing you did. The freeware vendor gets money from the PUP producer to do this, up to $2 per install.
Danger! Do not try this at home: download the top 10 apps on Download.com
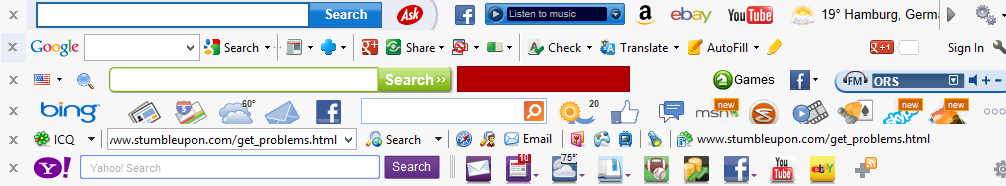
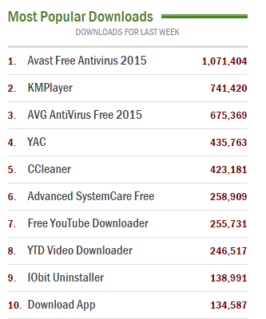
PUPs are not new. But its a very alarming trend that more and more large freeware vendors and distributors, such as download portals, are distributing PUPs in high volume – all in exchange for quick cash. Even Sourceforge, a hosting platform for open source projects, started to add PUPs to their downloads, without the consent of the developers who run their projects there. Tech website HowtoGeek recently showed what happens when you download the top 10 listed apps at Download.com ranked by download volume:
“We installed the top 10 apps from Download.com, and you’ll never believe what happened! Well… I guess maybe you might have a good guess. Awful things. Awful things are what happens. We’ve been railing against freeware download recommendations for years, so we thought, why not have some fun and see what really happens if you download software like a regular clueless user might?”
The result of this test: ALL the top 10 apps on Download.com come with bundles or PUPs, some loaded with them. HowtoGeek even recommends users to not do this at home on your primary PC, unless you want to make your computer a “smoking pile of useless.”
Antivirus programs have joined this nasty game too
Now, here is the top 10 Download.com list that HowtoGeek used for their test:
Does anything stand out to you on this list? There are two antivirus programs on there! Ethics in the software industry seem to be lost completely when even antivirus vendors bundle PUPs with their software. Now look at the download amounts in the above screenshot: up to one million downloads a week. Add to that downloads from other sources, and the fact that PUP producers are willing to pay anything from a few pennies to USD$2 per install, and it can give a rough idea how much money there is involved in this business: thousands if not millions of $$$. We learned that before as well when Emsisoft got approached for a similar PUP bundle deal.
Fact: 7 out of 8 tested free antivirus suites bundle with PUPs
We decided to further look into this and test other free, full antivirus suites. For reference, we downloaded the products in the test directly from the source (vendor website) and not from a download portal. The results are pretty shocking:
All tested free Antivirus programs come with toolbars or PUPs of some sort – except Bitdefender Free. A lot of them have a “rebranded” Ask toolbar that generates considerable pay per install (PPI) revenues while they’re labeled as part of the vendors own security solution. Some disclose they use Ask (for example Avira), others like AVG go as far as adding pops with coupon deals.
Antivirus programs are supposed to protect your computer from viruses, yet many of them give you a questionable program during installation, without clear disclosure. Below is the list of 8 free antivirus programs and the type of PUPs they give you during installation at the time of posting. Please note that we only included full antivirus suites, not scanner-only products.
![]() Bitdefender Free: as mentioned before, Bitdefender Free is one of the only clean antivirus vendors that does not come with any PUPs.
Bitdefender Free: as mentioned before, Bitdefender Free is one of the only clean antivirus vendors that does not come with any PUPs.
![]() Comodo AV Free: changes home page and search engine provider to Yahoo during the installation process, unless the user unchecks the box.
Comodo AV Free: changes home page and search engine provider to Yahoo during the installation process, unless the user unchecks the box.
![]() Avast Free: offers Dropbox during installation by default, unless you uncheck the box. No toolbars are installed.
Avast Free: offers Dropbox during installation by default, unless you uncheck the box. No toolbars are installed.
![]() Panda AV free: installs Panda Security toolbar, yahoo search takeover and MyStart (powered by Yahoo) home page takeover. No product rebrands, at least the installer is clear that both are Yahoo products.
Panda AV free: installs Panda Security toolbar, yahoo search takeover and MyStart (powered by Yahoo) home page takeover. No product rebrands, at least the installer is clear that both are Yahoo products.
![]() AdAware free: installs WebCompanion by default unless user unchecks the box. Also installs Bing Homepage takeover and Bing search takeover by default, unless opted out. Discloses that AdAware offers these programs to keep the software free.
AdAware free: installs WebCompanion by default unless user unchecks the box. Also installs Bing Homepage takeover and Bing search takeover by default, unless opted out. Discloses that AdAware offers these programs to keep the software free.
![]() Avira free: offers Dropbox after installation. Takes over search with Avira Safe Search, which is a a white-labeled version of the Ask toolbar. Avira does disclose that it partners with Ask, and states that it “chose Ask.com to be our partner in bringing you the SearchFree Toolbar because Ask.com is one of many vendors whose products offer functionality which we believe our users will value”.
Avira free: offers Dropbox after installation. Takes over search with Avira Safe Search, which is a a white-labeled version of the Ask toolbar. Avira does disclose that it partners with Ask, and states that it “chose Ask.com to be our partner in bringing you the SearchFree Toolbar because Ask.com is one of many vendors whose products offer functionality which we believe our users will value”.
![]() ZoneAlarm free AV + Firewall: with Custom Install: Zonealarm homepage and search takeover.This is a rebranded Ask toolbar, which is not mentioned on ZoneAlarm’s website.
ZoneAlarm free AV + Firewall: with Custom Install: Zonealarm homepage and search takeover.This is a rebranded Ask toolbar, which is not mentioned on ZoneAlarm’s website.
![]() AVG free: installs Web Tuneup, including AVG SafeGuard. Sets AVG Secure Search as homepage, new tab page and defaults search engine. Toolbar is Ask powered, although this is not explicitly stated. Also offers AVG Rewards, which displays popup advertisements with coupons and deals.
AVG free: installs Web Tuneup, including AVG SafeGuard. Sets AVG Secure Search as homepage, new tab page and defaults search engine. Toolbar is Ask powered, although this is not explicitly stated. Also offers AVG Rewards, which displays popup advertisements with coupons and deals.
Popular ways for free Antivirus programs to make money with PUPs
Looking at the above screenshots, we can see that the antivirus vendors have a few popular methods to make money with PUPs:
- Search Engine Takeover: you now set your default search engine to the software vendor’s choice, there’s big money to make there. Just look at this company called Google.
- Ask Toolbar: do a quick search on Google for the Ask toolbar, and you’ll learn quickly why the first results page is full of “How to remove the Ask toolbar” and “How to get rid of the Ask toolbar”.
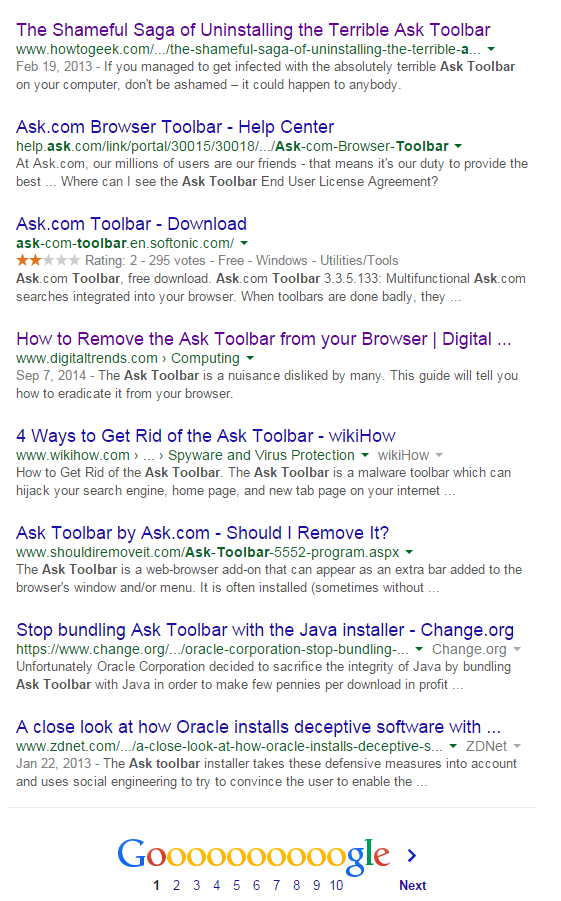
- Rebranded Ask Toolbar: even worse than the Ask toolbar, the rebranded version is a white-labeled Ask toolbar where the software vendor gives it a different name and look, while it’s just the Ask toolbar in disguise.
- Homepage take-over or new tab: “free” guaranteed traffic to a website anyone?
- Your data, search and browser behavior: it is not known what antivirus vendors do with your data. It is known that they are watching you and track you. Do you trust whether they do anything with this data? Tracking and selling browser data and other personal information has been a big business for years in the internet industry, so who knows.
What’s disturbing about all the methods these antivirus vendors use is that in the majority of the cases, the PUPs are included in the default intallation, unless a user opts out or reads the small fine print. Sometimes the PUP install is not disclosed at all, or hidden. It’s rarely explained what the installed PUP actually does, if anything. Questionable tactics to get onto computers of unknowing users.
When the product is free the real product is YOU
As HowtoGeek states as well, it doesn’t matter what download site you use. The people that make the freeware are the ones bundling. Some download sites bundle on top of that but it’s not the root of the issue. They’re a player in the game. As HowtoGeek states it in their article:
“There are also no safe freeware download sites… because as you can clearly see in the screenshots in this article, it isn’t just CNET Downloads that is doing the bundling… it’s EVERYBODY. The freeware authors are bundling crapware, and then lousy download sources are bundling even more on top of it. It’s a cavalcade of crapware. Each time we ran through this experiment over the last few months, different software would end up being bundled in a rotation, but every single software that bundles itself ends up bundling the same culprits: browser hijackers that redirect your search engine, home page, and put extra ads everywhere. Because when the product is free the real product is YOU.”
Do freeware users “enable” the PUP business?
Let’s clearly point out that not all freeware is bad and relies on PUPs, but the good ones have unfortunately become an exception to the rule. The few examples of good freeware are:
- Trimmed down versions of full products. where the free version gives an idea of the product and provides basic functionality while the vendor tries to sell a higher edition of the same software.
- The open source community. where people create software for fun or to help make the world a better place. Although this is a tricky one: sometimes others use open source projects to add PUPs by fake imitations.
- Projects that live off donations, although these have become rare.
 The rest of the freeware vendors need to resort to software bundles to make money. Are people enabling the growth and distribution of PUPs by continuing to download this freeware? In a way yes, but you can’t blame them really. Most of them just think a free piece of software sounds like a sweet deal, but have no clue what it may come with. At most you can blame them for the fact for not looking into why a piece of software is offered at no cost.
The rest of the freeware vendors need to resort to software bundles to make money. Are people enabling the growth and distribution of PUPs by continuing to download this freeware? In a way yes, but you can’t blame them really. Most of them just think a free piece of software sounds like a sweet deal, but have no clue what it may come with. At most you can blame them for the fact for not looking into why a piece of software is offered at no cost.
PUP producers know that what they do is misleading, freeware vendors know PUPs are highly questionable and antivirus vendors for sure know that it’s unethical. Therefore, all these players will go great lengths to hide the fact that they are bundling PUPs. They will make sure that they fulfill the legal requirements sharp, but use any possible way to increase the spread of those unwanted programs. The fact that vendors are willing to put their ethics aside and their reputation at risk for quick cash, says a lot. PUP distributors are taking advantage of the average “unknowing” computer user.
Conclusion: be careful with freeware, paid software usually doesn’t come with PUPs or bundles
The amount of PUPs will spread further and they will become nastier and sneakier in form if people don’t take action. The only way to make a change is collectively. Even if you are a PUP-free antivirus user, you are affected by the rapid growth of PUPs. You will hear about them more, see them blocked more, see more and more signatures updated to your antivirus program to detect all the different types of them. For example, Emsisoft’s malware analysis team now spends half of their overall analysis time on PUPs, while we could spend this time towards other resources and other types of malware to protect you from other internet threats. At least, users need to demand full disclosure so that they are given a chance to make a conscious choice whether they want to download a piece of software or not, and so that they know what they are downloading. Bottom line is, be careful with freeware, paid software usually doesn’t come with any PUPs or software bundles.
Did you ever find PUPs on your computer? Are you surprised by these PUP practices and the fact that freeware and antivirus vendors participate? Share your opinion and leave a comment below.
Emsisoft Enterprise Security + EDR
Robust and proven endpoint security solution for organizations of all sizes. Start free trialHave a great (PUP-free) day!
![Comodo-yahoo[1]](https://blog.emsisoft.com/wp-content/uploads/2014/12/Comodo-yahoo1.png)
![avast-dropbox[1]](https://blog.emsisoft.com/wp-content/uploads/2014/12/avast-dropbox1-456x319.png)
![panda-yahoomystart[1]](https://blog.emsisoft.com/wp-content/uploads/2014/12/panda-yahoomystart1.png)
![AdAware-wcomp-bing[1]](https://blog.emsisoft.com/wp-content/uploads/2014/12/AdAware-wcomp-bing1.png)
![Avira-safesearchext[1]](https://blog.emsisoft.com/wp-content/uploads/2014/12/Avira-safesearchext1.png)
![Avira-safesearchhome[1]](https://blog.emsisoft.com/wp-content/uploads/2014/12/Avira-safesearchhome1.png)
![ZoneAlarm-search[1]](https://blog.emsisoft.com/wp-content/uploads/2014/12/ZoneAlarm-search1.png)
![AVG-safeguard[1]](https://blog.emsisoft.com/wp-content/uploads/2014/12/AVG-safeguard1.png)
![AVG-safeguardChrome[1]](https://blog.emsisoft.com/wp-content/uploads/2014/12/AVG-safeguardChrome1-564x319.png)


