Beware! That Windows 10 update message could be ransomware in disguise

A new virus is on the loose and it’s targeting users waiting for their Windows 10 update. A variant of CTB (Curve-Tor-Bitcoin) Locker is currently being downloaded on to Windows 7 and 8 users at alarming rates. If you are waiting for your Windows 10 upgrade, please read the details below and proceed with caution when downloading anything from an email attachment.
It starts with an email
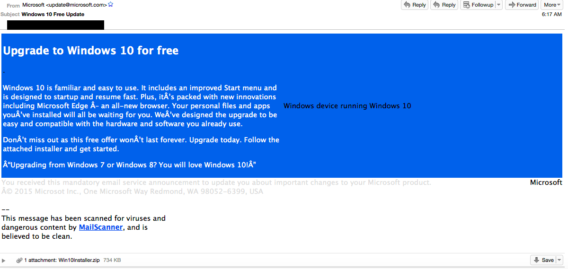
This new threat actor has a clever way of making its way onto your system. Since many people are eagerly awaiting their Windows 10 update, scammers developed a convincing email campaign to lure people into downloading their ransomware.
As you can see, the email has the appropriate color scheme as well as a believable email address: [email protected]. The scammers have even gone so far as to include a little note at the end that may give the recipient a false sense of security:
And then they demand you pay up
Once an unsuspecting victim downloads the false update to their computer and runs it, they’ll see this message:
The victim will find that their files have been encrypted and will not open properly, and like most ransomware variants, the decryption key will not reside on the infected system. The user allegedly has 96 hours before the decryption code is destroyed and the only way to get a hold of it before then is to pay an outrageous $200 USD.
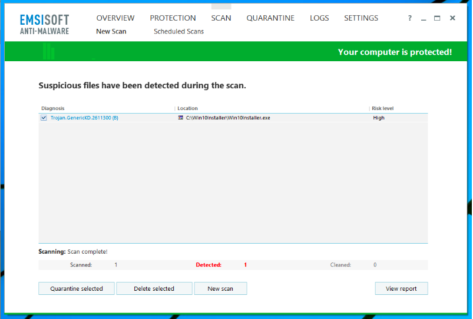
Early detection is key
As eager as you may be for the latest Windows 10 update, please be aware that so many cyber criminals are waiting to take advantage of you! Be wary of emails with typos, strange characters, and in the case of the phishing email above, an IP address from an unexpected part of the world (in this case, Thailand).
If you are suspicious of any communications you have had with a so-called Microsoft representative, contact customer support before moving the interaction forward.
If you haven’t already, equip yourself with the best anti-malware available. If you fear that you have downloaded the ransomware but haven’t run it, deploy Emsisoft Anti-Malware immediately and remove the nasty virus from your system!
Otherwise, stay vigilant online and make sure your back-up system of choice is up-to-date.
Emsisoft Endpoint Protection: Award-Winning Security Made Simple
Experience effortless next-gen technology. Start Free TrialHave a great, ransomware-free day!