Why every Android user should take the Stagefright leak very seriously

A vulnerability in Android called Stagefright was exposed at the 2015 Black Hat conference in early August. You may have heard of it, if only because the media frenzy that followed claimed that hundreds of millions of phones could be hacked with a single text – but is any of that true? If that were the case, surely Google, the developer of the popular operating system, would have fixed it by now…right?
What is Stagefright and why should you care?
You may have grown accustomed to all of the vulnerabilities, bug and alerts out there in technology land. You’re calm because you know that ultimately there will be a patch to fix it, right?
Unfortunately, it’s not so simple with the Stagefright leak. Think of a doomsday film where a deadly asteroid is about to strike Earth, and there’s no way for scientists to divert it with their fancy technology. That’s basically what’s going on – the Stagefright bug, due to the nature of the Android world, isn’t likely to be addressed any time soon. If things don’t change, it’s only a matter of time before an exploit strikes and brings chaos to an unthinkable number of devices.
So, yes, it is possible that you could receive a strange video text, not even open it, and some cyber criminal halfway around the world could start spying on you through your video camera. But that’s only one possibility.
If a hacker gets into your device through the Stagefright vulnerability, he could gain access to your address book, apps, message history, personal emails, and all the information tied to your Google account. This means that every bit of information tied to your Google account – from Gmail to Google Drive – is up for grabs: financial information, browsing history, personal messages and classified work documents…
It’s imperative you understand that your phone isn’t the only thing at risk. Your whole digital life is at risk.
How does Android work, exactly?
To understand the Stagefright vulnerability properly, it’s important to look at the Android architecture. Android is very modular operating system, so things run in separate processes. This is in part thanks to the Dalvik virtual machine, which is the component in most Android phones (it has been replaced entirely by Android runtime in Android 5.0) that allows each app to run separately and independent of the Linux kernel. This keeps apps from detrimentally interfering with each other or with the operating system.
 This means program processes rely on IPC or inter-process communications to work together. This is known as application sandboxing (or application containerization), and one of the alleged advantages of this is that keeping applications isolated improves overall security.
This means program processes rely on IPC or inter-process communications to work together. This is known as application sandboxing (or application containerization), and one of the alleged advantages of this is that keeping applications isolated improves overall security.
Stagefright is what processes media in Android’s MediaServer, written primarily in C++. It handles all video and audio files, and provides playback facilities. It also extracts metadata for the Gallery (like thumbnails or dimensions of a video).
How Stagefright reaches you
So it might be fair to assume that since the programs on your phone are sandboxed, most aspects of the system are safe from a single vulnerability. But while the compartmentalized nature of Android is supposed to keep programs from interfering, MediaServer is a very privileged service that has access to audio, bluetooth, camera, internet, and more. What’s worse, many phone manufacturers have given the Stagefright component system permissions on their devices, which is only a step below root access.
In layman’s terms: a hacker could gain access to your entire device.
An attacker only needs your phone number to conduct a successful hack. He or she could remotely execute code through a video sent via MMS. It would require no action on your part, as Android phones are set to preload videos. The attacker can even delete the message after sending it, leaving you with little more than a mysterious notification.
If that doesn’t sound horrifying enough, that isn’t the worst of it. The reality is, that’s just one way that the vulnerability can be exploited. It’s up to the hackers of the world to discover the rest.
Who figured this out?
Joshua J. Drake, an Android security expert, is the man behind the research. He is the Senior Director of Platform Research at Zimperium Enterprise Mobile Security, and the Author of “Android Hacker’s Handbook”. He’s also the founder of the #droidsec research group, an Android-focused research community.
With the support of Zimperium and Optiv, Drake conducted this security research, using his “droid army” – a collection of 51 Android devices. You can learn more about how he conducted his research in his presentation at the Black Hat conference in Las Vegas.
A fragmented Android world
Android is one of the world’s most popular operating systems and it has a unique story. The rate of development is incredibly fast, but that development doesn’t come without a price. Since original equipment manufacturers and carriers are able to adapt the operating system due to its open source nature, this leads to a number of iterations that have unique update and patching needs – over 24,000 models currently exist in the Android ecosystem.
The biggest problem with this vulnerability, as Ars Technica writer Ron Amadeo points out, is that original equipment manufacturers have been able to adapt the Android code to work with their devices. This creates a dilemma where an unthinkable amount of patches would have to be made in order to successfully protect the majority of Android phones out there, and no single company, team, or entity is responsible for getting this issue under control. Because updates will focus on newer phones, and many patches will be dependent upon a myriad of manufacturers and carriers to distribute them, it is possible that millions to hundreds of millions of devices will remain vulnerable indefinitely.
What’s being done?
Google, as well as number of manufacturers and carriers have responded with patches for the following devices.
Zimperium has also launched its ZHA Alliance to address the issue of communication between relevant manufacturers and carriers on the issue. As Zimperium so aptly stated, “According to our understanding of the Android ecosystem, security issues reported to Google are only shared with active partners”.
Zimperium has also released an app known as the Stagefright Detection app, which can help you identify if your phone is actually affected by the vulnerability.
So what’s the problem?
You might think that since the patches are rolling out, there shouldn’t be any further problems. Surely the patches will trickle down to older phones, and Zimperium will help facilitate that communication between Google, carriers, and manufacturers
Even if that is the case and the majority of phones get patched up, there may be an issue with the effectiveness of Google’s first patch. Security researcher Jordan Gruskovnjak at Exodus Intelligence has reported that the initial patch released by Google was inadequate. The Exodus team was able to craft an MP4 that could bypass the patch. They even claim that Zimperium’s Stagefright Detection app will green-light your patched phone, even though it’s still vulnerable.
Google has responded to the situation, asserting in a statement to The Verge, “We’ve already sent the fix to our partners to protect users, and Nexus 4/5/6/7/9/10 and Nexus Player will get the OTA update in the September monthly security update”.
If that wasn’t bad enough, Rob Miller from MWR Labs has found another vulnerability that can bypass the sandbox mechanism. Originally reported back in March, it seems that Google has yet to release a relevant patch. Researchers at Trend Micro have claimed to have also found a vulnerability, this time in Android MediaServer, which they reported to Google back in June (Google published a fix in early August).
The reality is, even if Google’s next patch is effective it doesn’t address the full story. The Stagefright media circus simply revealed a can of worms that opened long ago – Android has some major security flaws, and the broken chain of distributors and manufacturers makes it nearly impossible to rectify.
What you can do
If you have an Android phone with version 2.2 or higher, it may seem that there isn’t much left in your control. But we encourage you to do all you can to take security into your own hands.
While it’s true that there are limits to your autonomy in the face of all of the vulnerabilities your phone could be riddled with, there are several steps you can take to make your experience on Android safer. Even if you don’t have an Android phone, you can use these tips and apply them to your own smartphone experience.
Change your settings
It’s important to acknowledge that while Zimperium illustrated an exploit through MMS and that’s what the media has held onto, this is just an example of how the vulnerability can be exploited, so disabling auto-retrieval will not necessarily protect you from all possible hacks. Joshua J. Drake himself said at the Black Hat conference that the Stagefright bug is exposed via multiple attack vectors.
With that being said, the MMS attack has been receiving a lot of attention, and it’s possible that cyber criminals are getting ideas. So it’s best to deactivate auto-retrieval as it preloads videos and messages for you. Here is how to disable the auto-retrieval feature on the most common messaging applications:
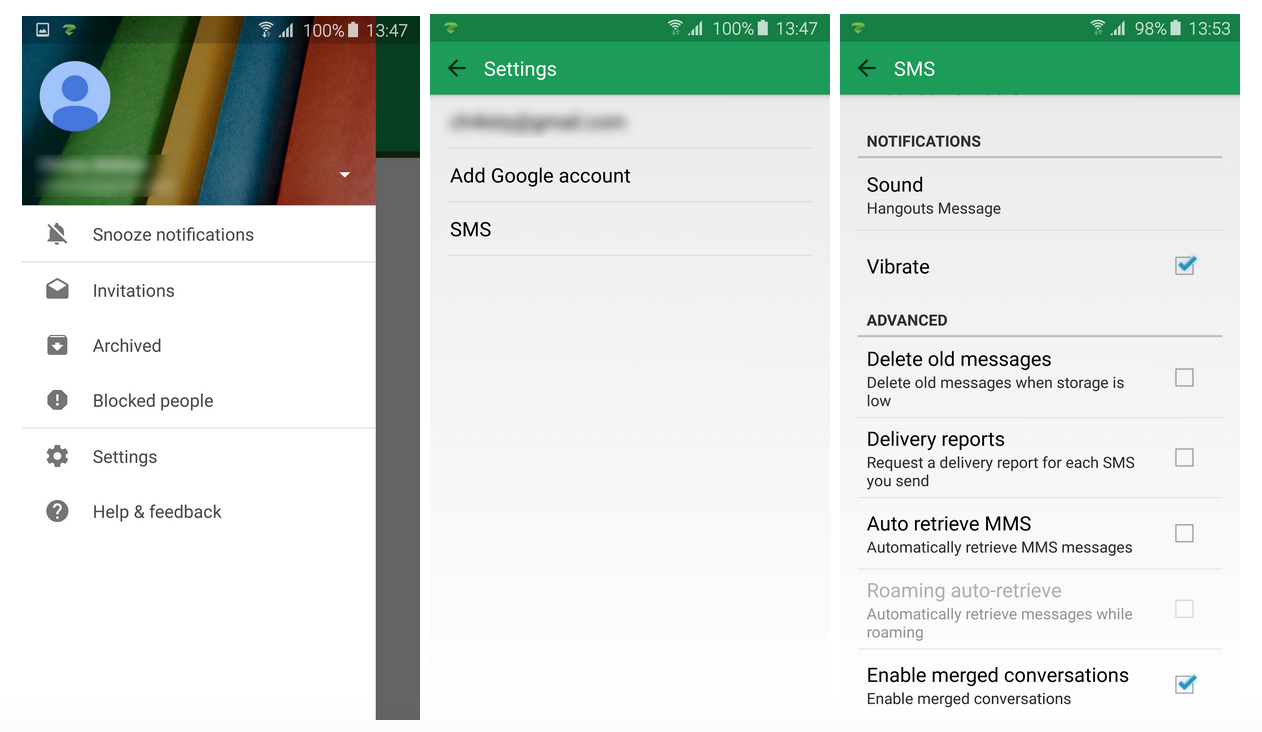
Google Hangout
Open the app and select Settings by tapping the three horizontal lines in the top left corner. Click the Settings wheel and then select SMS. Uncheck Auto-retrieve MMS.
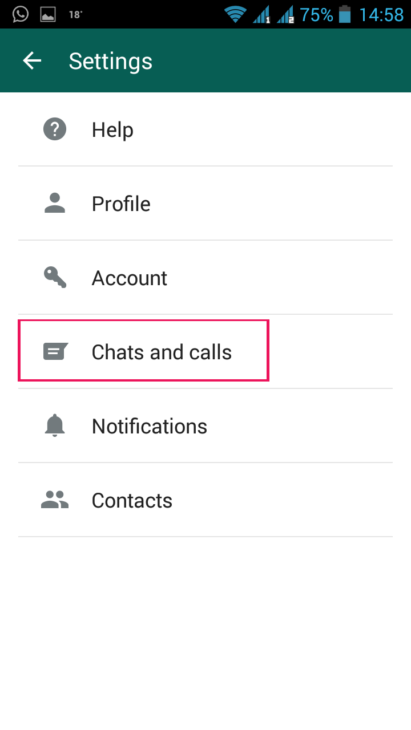
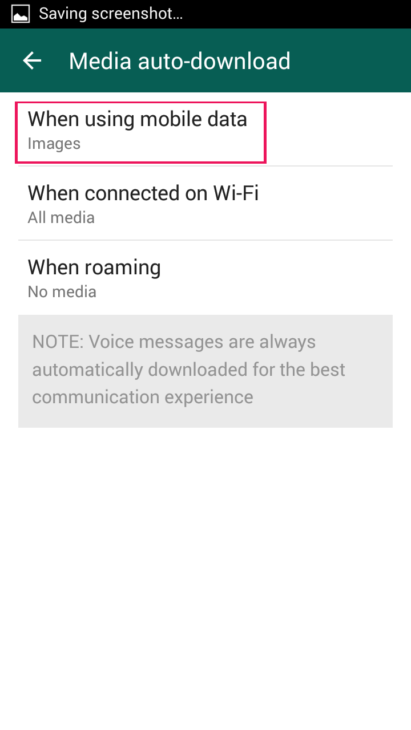
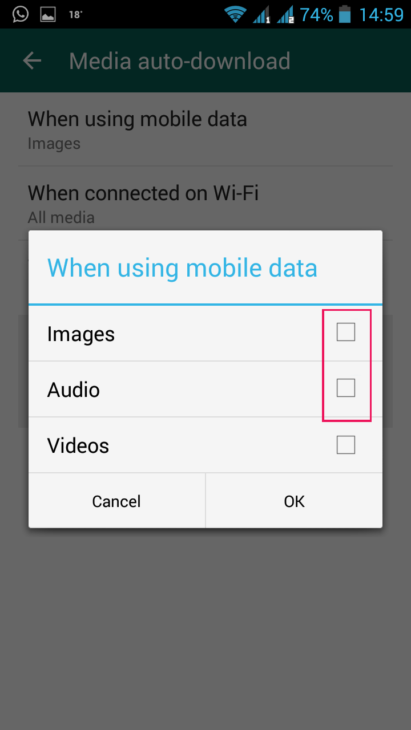
Select Settings by clicking the three dots icon, and then select Chat Settings. Tap Media auto-download and go to the When connected on Wi-Fi. Deselect videos, and then do the same under the When using mobile data option.
![]()
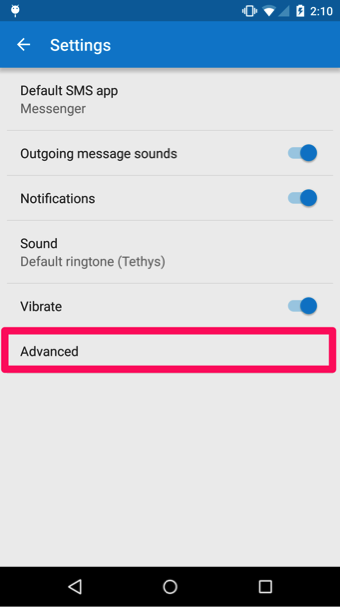
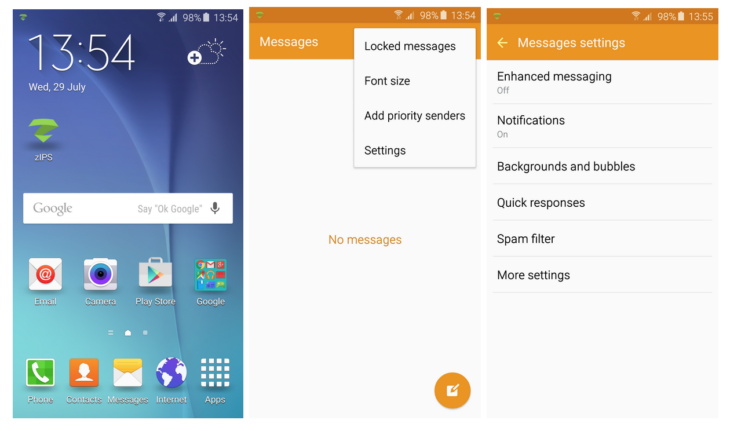
Google Messenger
Touch the three vertical dot icon in the upper right corner. Select Settings and then Advanced. Then deselect Auto-retrieve.
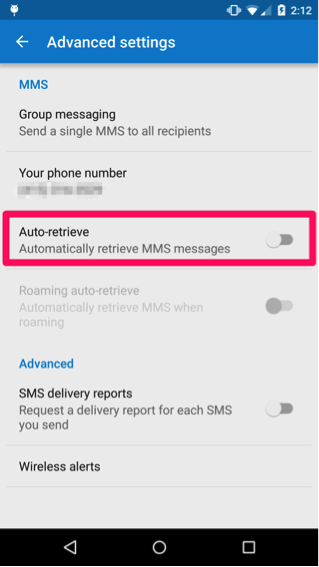
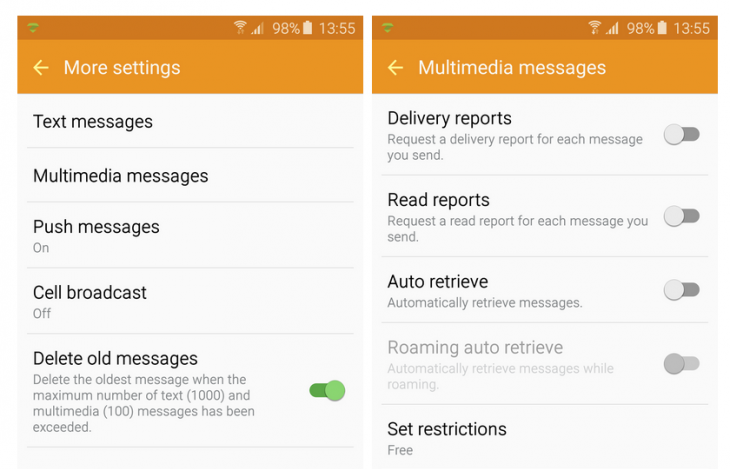
Messages
Navigate to More and select Settings, then More settings. Click Multimedia messages and then slide the Auto retrieve toggle to the left.
Even after deactivating auto-retrieval, be wary of manually loading an MMS from an unknown source, and if you want to be extra safe, don’t load one from friends or family either. They can unknowingly put you at risk if their phone is compromised.
Your consumer choices
While most normal people don’t have the resources to buy the latest and greatest model of every device, it’s important to consider the likelihood that future devices will be more secure than current models. Additionally, important security patches and updates generally won’t be released to devices that can’t support newer versions of Android.
Remember to educate yourself on the operating systems and programs you use, and vigilantly update to newer versions if possible. For example, the Mozilla Firefox browser was also affected by the Stagefright vulnerability, but the issue has been rectified since version 38.
Make your voice heard
Just because the mainstream media has dropped the issue as of late doesn’t mean the Stagefright bug doesn’t affect millions of people around the globe. Voice your own concerns and demand that your carrier keep you updated on the issue.
Make noise on your social media channels and tag Google, your carrier, and your manufacturer in your posts. Forward articles related to the Stagefright issue to your Android-using loved ones.
Switch your operating system
This is an option for more experienced users and not a recommendation for most people. Still, it is an option and should be discussed with more regularity. If your inclined to try this option, consider using firmware with a regularly updated ROM, such as CyanogenMod.
You will need to root your phone, and if you do this you will most likely lose your warranty with your manufacturer. Also be aware that this move will not make you 100% clear of the Stagefright vulnerability or other bugs. The advantage is that you have an Android device, but the hassle of waiting on manufacturers and carriers to adapt patches is removed, and you can receive updates more immediately.
As the months go by, we can only hope that there is a real solution to this issue. Remember to stay informed about security updates, subscribe to newsletters, and follow security blogs. Talk to your friends and family, and assert your rights to privacy and safety as a consumer. While developments in technology move at an impressive rate, there’s no point in having all of these fancy devices if we’re moving towards a digital Armageddon. Remember, safety is just as important as progress.
Emsisoft Enterprise Security + EDR
Robust and proven endpoint security solution for organizations of all sizes. Start free trialHave a great, exploit-free day!