Public Wi-Fi – is it safe?
Stuck without a data connection while you’re out and about? Free public Wi-Fi offers you quick access to the internet in airports, cafes, hotels, main street hotspots, even fast food chains. Burger, fries, and Wifi password please! You can work or play while you wait and, best of all, it’s free. But is it secure? The clue is in the name – ‘Public’ not ‘Private’ Wifi.
When you access a website, it usually needs 10-30 computers in-between to send the data. A typical route is that you connect to your router, your router connects to your Internet Service Provider’s (ISP) main router. That router connects to an international overseas router, then that one to the main datacenter core router, and finally to the destination webserver.
It sounds complicated, but basically, each of those machines, or hops, processes your website request and passes it along until it reaches the destination server, or website, you were accessing.
 So, what’s the danger?
So, what’s the danger?
At each one of these hops, your data is received and moved along. If this data is unencrypted, each hop can also log in and watch it. So, you should automatically assume that everything you do while connected to a public Wifi network is able to be seen. Further, cyber-crime is ever-changing but there are three very specific recurring threats facing public Wi-fi users.
Man-in-the-middle attacks
This is where someone on the same public network is able to get their PC between you and the destination webserver (the website). If positioned correctly, a web pickpocket can simply pluck your passwords, emails, documents, even your logins, from the air. Instead of skulking in back alleys, now the Artful Dodger sits comfortably with a laptop, software and a cup of coffee while you pay your bills online as they watch. If they are able to intercept passwords and usernames, these elusive men-in-the-middle can also do some amateur theatricals known as spoofing.
Spoofing is when a con artist impersonates someone else and starts a conversation with you. They can even impersonate you to someone else at the same time and be in the middle of a correspondence, opening up all sorts of nasty possibilities. For example. Any router hop (one of the ten to thirty computers we mentioned before) between source and the destination computer may ‘pretend’ to be the destination computer for say, PayPal.com. When your browser connects to the this hop, it expects that the response is actually coming from PayPal. It checks the server certificate to see if it is from a Trusted Root Authority such as Verisign. But if someone has hacked the certificate authority, when you arrive at this hop, your computer may be infected with malware that makes your computer believe it that the Server Certificate is Authentic when it isn’t. It will show green and away you go with your credit card details only to have them sent straight to a cyber-criminal.
Sniffing
Sniffing involves similar technical access, but is instead the constant monitoring of public network traffic, grooming for passwords and interesting data. It’s electronic snooping that needs only some software on a laptop and a certain lack of morality. Just one of the things they can steal is the session cookies that keep you logged on to websites that retain passwords and credit card information, such as Ebay, Mail and Amazon. A bloodhound is sniffing and stealing your private data. That person with the laptop in the corner might not be on Facebook after all.
Malware Invasion
Malware is malicious software downloaded to your PC over a network. It gives someone access to your computer without you even knowing it. For instance a hacker can set up a Wifi network with a name just like the one you’re expecting. You look up ‘Joes Cafe’ instead of ‘Joes,’ innocently log on and now the hacker can access your computer and install their malware to record your passwords, send you to unsafe websites or send 1000 spam emails from your Outlook account.
Though the threat landscape is rapidly changing, there is some good news. You can prevent Malware invasion with a top grade anti-malware program.
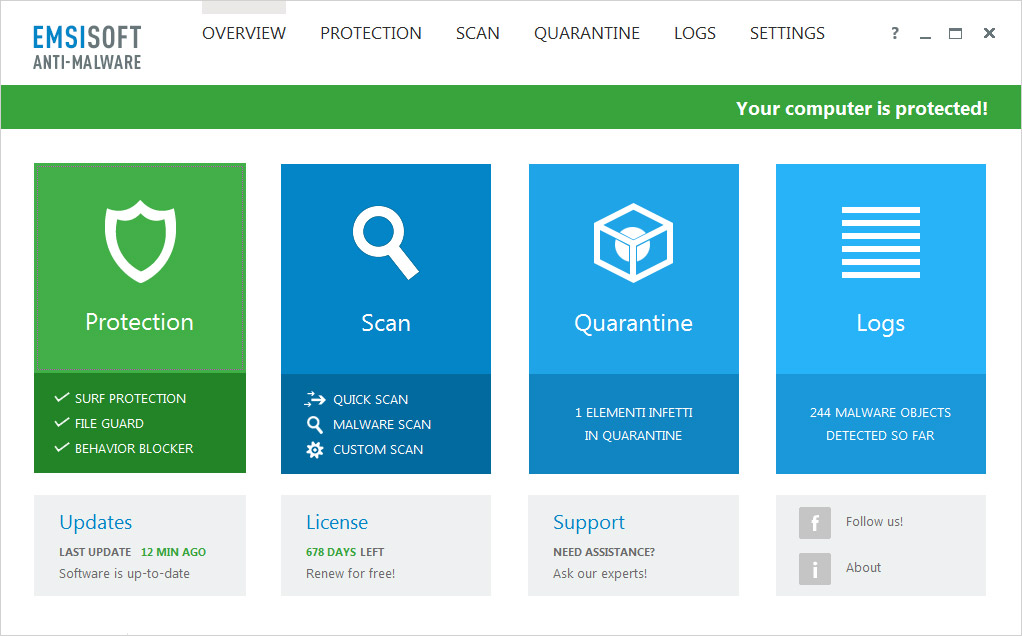 Emsisoft Anti-Malware
Emsisoft Anti-Malware
Let’s look at what you can do to get some protection from man-in-the-middle and sniffing attacks too.
How do you protect yourself?
- Small settings changes: Select the option to use authentication and SSL in Outlook’s advanced email settings. This creates an encrypted link to help keep your emails private. If you’re using a webmail service check with that service how to add SSL encryption or look for HTTPS in the web address, a standard encryption protocol that delivers your information privately.
- Turn file sharing off in the advanced network and internet settings. If you’re usually working in an office where you share files then turn this off when out and about – it’s an open invitation for sniffers!
- Turn your Wifi off when you don’t need it.
- Check the name of the network is correct. Sniffers set up their own hotspots hoping you’ll log in and show them everything.
- Only use https websites for secure information. The ‘s’ added to the http shows that the connection is delivering the data securely by using SSL – a secure encryption protocol. Any website that requires sensitive information should use SSL and be identified by the https: at the start of the website address, like our License Centre:
- Use cell data for sensitive browsing. If you’re doing anything you wouldn’t want someone snooping on, such as internet banking or online shopping where your credit card details are required, use your own laptop data, or your cellphone’s personal hotspot.
Extra security measures you can take
Software – keep your software up to date so you don’t get download requests on the move. If you do get requests be very very suspicious. Ensure you are running, and regularly update quality anti-virus software.
VPN – a Virtual Private Network service channels your data through their encrypted tunnels so it is secured from prying eyes. Do some homework first. Learn what suits your needs best and understand how it works. It isn’t a complete solution, and they’re still susceptibilities, but it does help.
Firewall – your built in Windows firewall can help stop others accessing your PC, which is good. But it won’t protect the data you are transmitting over the public wifi. Still, it adds an extra layer of protection.
A word on Encryption
Public Wifi often boasts localized encryption. Additionally, you can run an encryption programme on your laptop to encrypt data transfers. But what do these two options actually offer?
Many public Wifi networks now use WPA2 encryption. This secures the wireless transfer from your computer to the local router at the heart of the Wifi hotspot. That’s good, but what happens next isn’t. The router then sends your data to the internet with no encryption. It’s at this point someone can sniff or record it. Unfortunately, our data is still not safe.
You can also use various encryption tools on your laptop. For instance you can encrypt a folder or file in the advanced tab of its properties. You can also set Outlook to encrypt emails which can then only be read by someone with whom you have shared certificates. Microsoft’s BitLocker is built in to Windows and can encrypt your whole hard drive. Additionally, you can use browser based tools to encrypt online email clients.
But all of these tools needs a good level of knowledge and experience to use effectively and without that they may provide a false sense of security. Like some of those electrical goodies you buy really cheap online with an instruction manual of 100 pages of incomprehensible English, it simply is just not that easy. If you don’t know how it works, you won’t know if it’s even working. Our sage advice is not to use them.
 The last word on keeping safe
The last word on keeping safe
We’ve discussed some settings you can adjust on your laptop, and some simple things you can do to help keep your data safe.
If you still really need to use public Wifi for everything we’ve suggested three security measures you can take.
But ultimately the four things that will keep you safe on public Wifi networks are:
- Don’t use public Wifi for any sensitive information. Turn it off and use your own mobile broadband.
- Have the latest and best anti-virus and anti-malware protection installed and regularly updated, such as Emsisoft Anti-Malware.
- Install and run Emsisoft Internet Security. Its firewall helps to keep your PC invisible to others on public wifi.
- Clean your computer regularly with the Emsisoft Emergency Kit which can be used without installation.
Have a happy (malware-free) day!
Your Emsisoft Team.
Emsisoft Enterprise Security + EDR
Robust and proven endpoint security solution for organizations of all sizes. Start free trial