WannaCry Ransomware: Interview with Emsisoft’s ransomware experts


There is so much news surrounding the WannaCry Ransomware outbreak that it is impossible to know where to start reading. As mainstream media outlets are jumping on any new information that may or may not be connected, some articles even raise more questions than they answer.
The fact is: WannaCry ransomware has hit hundreds of thousands of computers since it began spreading on May 12th, 2017, and it has caught the world’s attention like no other.
But what makes this ransomware infection different to any other? How did it spread so fast? And what can we expect in terms of future ransomware attacks?
To find out, we sat down with Emsisoft CTO and Head of Malware Lab, Fabian Wosar, and Emsisoft Ransomware Researcher, Sarah W., to break down the confusion around WannaCry, how to protect against it and why backups are more important now than ever.
Thank you for taking the time to talk about WannaCry and how it affects our customers. To start off: Why is this ransomware different to other strains and how has it spread so fast?
As part of our daily job, we monitor a lot of different channels to identify and track ransomware activity. Those include our malware and research feeds, community channels like forums, ID Ransomware and Twitter. Friday morning our attention was drawn to a lot of activity on Twitter that was WannaCry related.
We soon started to realise that this wasn’t a normal ransomware outbreak when we saw how the NHS was hit and the rate at which entire networks were impacted.
How WannaCry spread
The ‘Eternal Blue’ Windows vulnerability [an exploit discovered by the NSA and kept under wraps] was leaked among a series of others by The Shadow Brokers hacking group in March 2017. WannaCry uses a type of worm that spreads rapidly across networks via this vulnerability that is present in older, unpatched Microsoft operating systems such as Windows XP. Typically, ransomware is downloaded to one computer at a time. However, with this worm, once it is inside a network it spreads like wildfire from computer to computer, without any action from the computer’s user.
This issue was actually patched by Microsoft in March 2017, meaning the worm only impacted computers with out-of-date operating systems. This is typical of hospitals which are bound to existing hardware that is not built to handle modern operating systems, yet are always connected to the internet.
Because this worm only impacts computers that have not had the most recent Windows update installed, any vulnerable computer open to the internet is at risk. This is why we always stress the importance of keeping all software, especially your operating system, up to date.
Compared to other global ransomware attacks, how sophisticated is WannaCry?
WannaCry as a worm is only remarkable because of the NSA exploit (Eternal Blue) that it uses. However, that exploit code wasn’t written by the malware author, but was pretty much a copy and paste job. There is nothing sophisticated or impressive about copy and paste.
Other than its worm-like behaviour, WannaCry is nothing special in terms of ransomware. If anything, it is rather unsophisticated.
But this is a big issue for victims. The code used to generate an individual bitcoin address for each user was not enabled, meaning that there are 3 bitcoin addresses to be shared between all victims.
The criminals will have almost no idea which victims have actually paid. Since there is no automatic decryption based on an individual’s bitcoin address, the chances of having your files decrypted after payment are very low.
Since the outbreak, security researchers have been able to find a “killswitch”. Can you explain what this means exactly?
Essentially, malware doesn’t like to be found in people’s systems as this permits forensic analysis of the code which may ultimately lead to the criminal who developed it. By its very nature, malware often tries to avoid analysis by attempting to detect the artificial environments, usually referred to as “sandboxes”, that are set up by researchers to observe and manipulate malware samples running on a system.
Sandboxes are usually isolated from the internet, but a lot of malware requires some kind of access to the internet to function properly. So, sandboxes often simulate an artificial internet, where every connection to the internet always succeeds and every internet address returns something useful.
One method malware uses to detect such an environment is to just try to access an internet address it knows doesn’t exist. If all of a sudden it can, it assumes it is being executed in such a sandbox. The malware quits whatever it is doing so it can’t be observed and looks like a harmless program; this is what’s referred to as ‘killswitch’.
Usually, these checks are done by generating domain names at random, but in this particular case, the WannaCry ransomware author decided to use a hardwired domain name. When it was registered by a fellow researcher, it became accessible via the real internet as well. So, for the malware, every system with a direct connection to the internet looked like a sandbox. The malware simply shut down, thinking it was being observed.
Yet it is still unclear if this killswitch was intended by the WannaCry author or not. What we do know is that the ransomware hasn’t changed at all, and neither has the worm that is spreading it. Until now, there is no confirmed sighting of a truly recompiled and fixed worm component that uses a different kill switch, apart from a few manually edited ones that have never reached the same distribution of the original.
Do you expect further ransomware attacks based on these exploits?
Almost certainly. We don’t doubt more criminals will be using a similar worm to spread malware, including possibly more ransomware. In fact, a bitcoin miner was already spread this way. Given that we have seen other ransomware, such as Spora ransomware, in the past that has had much more sophisticated payment methods, it is not really a question of “if”, but rather “when” we will see a global ransomware outbreak what will be even more “successful” and costly to its victims.
Learn more about common ransomware infection methods
Is there a way to decrypt your data once you have become a victim of the WannaCry ransomware?
Unfortunately not, as WannaCry uses secure encryption. Even if you pay the criminals, as I mentioned above, they have no way to track payments, so you may not get your files back and instead be asked for more money.
Emsisoft customers were not affected by the attack. Can you explain how, and why in other cases, security software was not able to detect the threat?
In some cases, I would think that victims were simply not running an antivirus or any kind of security software. In the cases where people were running security software, it’s possible that the product’s ransomware behaviour detection may be slightly lacking.
Emsisoft’s products in particular use a layered approach when it comes to protecting our users. We believe that no technology on its own is 100% fool proof. However, by applying multiple different technologies, a very high degree of protection can be achieved. In the case of WannaCry ransomware, Emsisoft customers stayed protected from the beginning via a 3-layered approach:
- Firewall: If you were using Emsisoft Internet Security, the firewall inside it would have prevented someone from the outside accessing your port 445, which is the port the vulnerable SMB protocol listens to by default and that the WannaCry worm contacts to exploit. If the port can’t be accessed, no exploitation takes place, so your system is completely protected from the malware.
- File Guard: The moment before the worm becomes active on the system, the File Guard will check it against our signature database. Our generic signatures that we created for the WannaCry outbreak back in February did cover most of the variants used in this attack as well, so the attack was stopped. The few variants of the worm component that weren’t already covered were added within 30 minutes.
- Behavior Blocker: Once the worm component becomes active, the behavior blocking technology will step in, detecting the malware’s attempt to infect the local system as well as the attempt to infect other systems on the network. Similarly, once the ransomware component becomes active, Emsisoft’s Behavior Blocker will detect the ransomware-like behaviour and stops it in its track.
So our products are designed with failure in one layer in mind, as we don’t subscribe to the philosophy of putting all of our eggs in one basket. Even if one layer doesn’t stop the infection, there are others to step in.
That being said, no product will detect everything. This is why securing your system and making backups is important.
How at risk are consumers and business following this attack, and what else can be done to protect against a future ransomware outbreak?
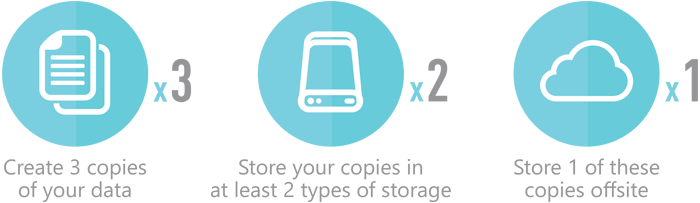
The 321 backup philosophy is the best protection against ransomware:
Keeping on top of updates for your operating system and all high-risk applications (applications that either access the internet directly or that are used to edit or view documents originating from the internet/email, like browsers, PDF viewers, media players, email clients etc.) is the second most important thing.
Yes, updates can break things sometimes. However, having proper backups mitigates those dangers as it allows a user to simply restore the previous version easily just in case something does break. Backups are awesome like that.
Last but not least, using an up-to-date anti-malware software helps to mitigate the vast majority of all malware, so use it. Using some kind of firewall, either in form of a router or the built-in Windows firewall, helps to mitigate worms like the WannaCry one by isolating potentially vulnerable services from the internet.
Have a nice (WannaCry-free) day!