That video post in Craigslist!
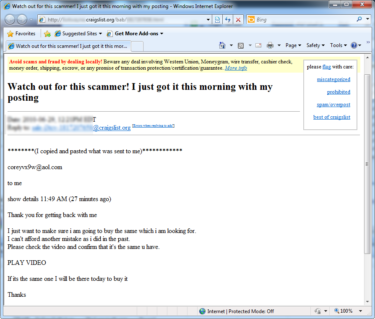
Craigslist is one of the most popularly visited website, and malware authors are always on the lookout for such vectors for their own interest. A message like below have been circulating around in craigslist
I just want to make sure i am going to buy the same which i am looking for.
I can’t afford another mistake as i did in the past.
Please check the video and confirm that it’s the same u have.
PLAY VIDEO
If it’s the same one I will be there today to buy it
Few have already fallen for this and one such shows.
The video url points to
• http://fav-vid.net/playvideo.php?video=jgahnYYNPe0
• http://watch-stuff.us/playvideo.php?video=jgahnYYNPe3
The contents when analysed exposes
![]()
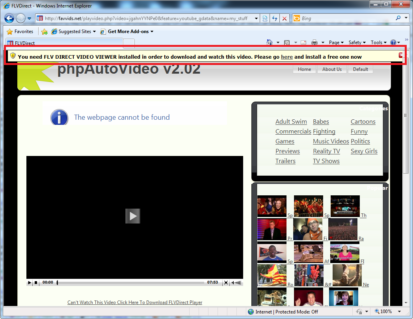
which redirects users to the following hyperlink hxxp://favvids.net/playvideo.php?video=jgahnYYNPe0&feature=youtube_gdata&name=my_stuff
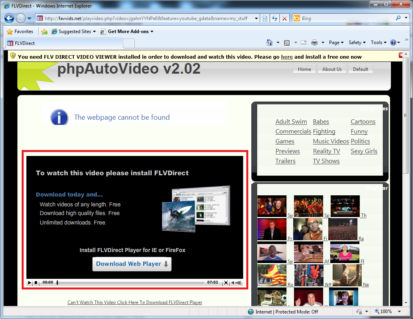
The website when visited plays an old trick. The video is shown as not loaded and an additional action has to be taken to see the video.
The confused end user goes on to install the malicious file thus falling into the malware author’s trap.
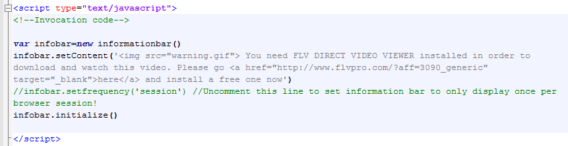
The following code executes the action and when user goes on to press “Play”
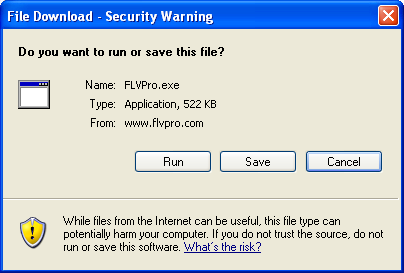
the download request comes for FLVDirect player, if user agrees redirected to flvpro.com.
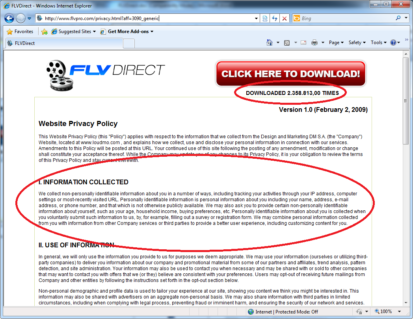
The privacy page clearly mentions the collected information such as IP address, computer settings etc. The other interesting information is the number of downloads for the specific file, which is more than 2 million thus playing as a confidence booster. Let’s go a bit deep and we see the following
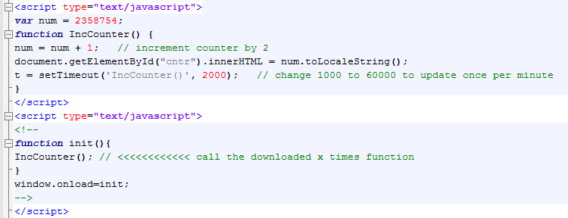
The script makes the download count to start from 2358754 and continues to grow with every second. Another trick to fool users. The scan reports for the same is shown below.
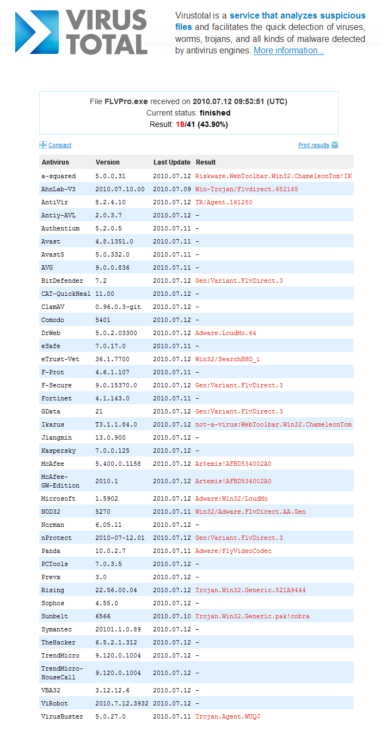
We at Emsisoft make sure to remain a step ahead always, detecting the specific malware as Riskware.WebToolbar.Win32.ChameleonTom!IK.
Further analysis on the malware was done. When executed this adware, the following installation screen appears.

The user goes on to “Accept and Install” and the program goes on to change browser settings without user knowledge, and default homepage changes to hxxp://flvdirect.iamwired.net
The following remote website connections were established while installation
• download.flvmeganetwork.biz/FLVPlayer_silent.exe
• submit.flvmeganetwork.biz/usr/getgeoipinfo.php?gup=XnqtpZBVQQk=&u={AB4BB94A-733E-4B06-96A9-91C327FB0976}
• flvmeganetwork.biz/smb/fknst.php?v=1&p=oQ9M8bwrbWN7oktDK0105%2BSIZy%2FRfnOOWdfskwm4fggJrfJePi8zqEP%2Beq7a0FziayoOdCG1c54%3D
•flvdirect.com
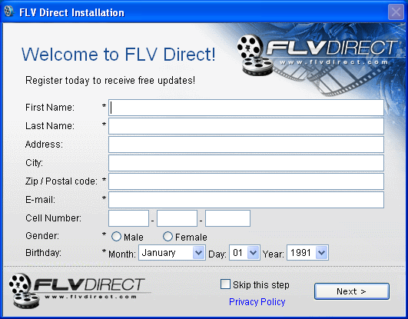
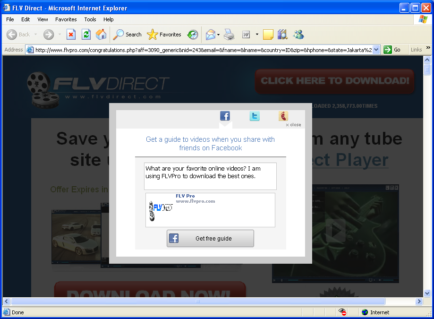
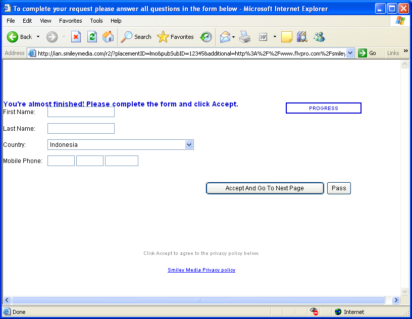
Once user goes on to fill up informations as shown, popups start appearing
The browser when opened , the following homepage starts as default with a new shortcut at desktop.

When the application is run , the player opens as below.
Emsisoft Endpoint Protection: Award-Winning Security Made Simple
Experience effortless next-gen technology. Start Free Trial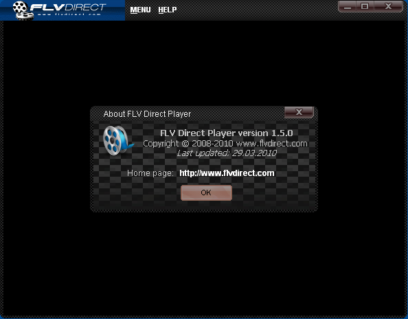
The Register has also reported about the specific adware and can also be installed through mishandling in facebook. Make sure to keep Emsisoft AntiMalware updated and be safe.