Fake Facebook worm spreading through Yahoo, IRC
In between email spams, twitter, facebook let us not forget one of the most prevalent medium a malware can spread around. Messengers have always been a popular medium for malware propagation and we at Emsisoft Labs recently came across worm like behavior attempting to spread through Yahoo! Messenger.
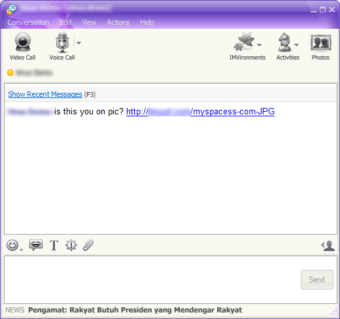
The initial picture is not too unfamiliar to someone using Messenger, with the popup of a random message window “Is this you on pic? Hxxp://hyperlink.
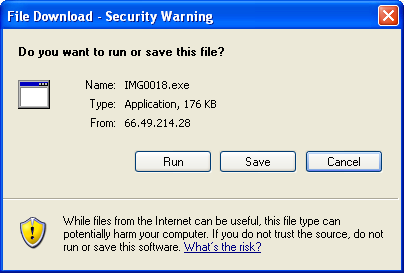
If the victim clicks the hyperlink, the default browser opens and download file prompt appears. We found out the following few common executable download links
- PI6-JPG-www.facebook.com.exe
- PIC007-JPG-www.facebook.com.exe
- PIC67576-JPG-www.facebook.com.exe
- PIC676-JPG-www.facebook.com.exe
- PIC6781-JPG-www.facebook.com.exe
- IMG0018.exe
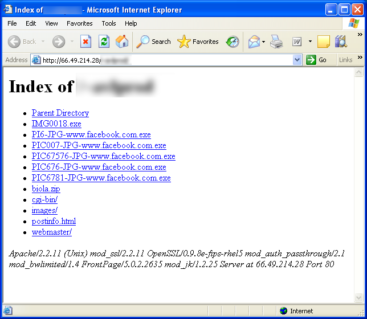
Analysing further we see the parent urls as below
- hxxp://75.102.36.231/*****45336-JPG-www.facebook.com.exe
- hxxp://migre.me/*****?=www.facebook.com/photo.php?=
- hxxp://66.49.214.28/~av***/IMG0018.exe
- hxxp://66.49.214.28/~av***/PI6-JPG-www.facebook.com.exe
- hxxp://66.49.214.28/~av***/PIC007-JPG-www.facebook.com.exe
- hxxp://66.49.214.28/~av***/PIC67576-JPG-www.facebook.com.exe
- hxxp://66.49.214.28/~av***/PIC676-JPG-www.facebook.com.exe
- hxxp://66.49.214.28/~av***/PIC6781-JPG-www.facebook.com.exe
On execution of the malicious file, it opens browser to http://browseusers.myspace.com/Browse/Browse.aspx which disguises itself running its own malicious activities in the background.
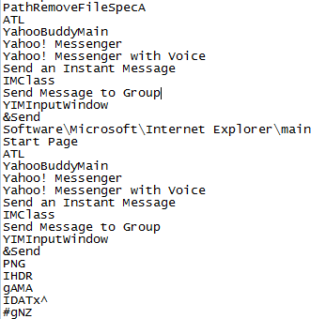
We did some initial research, and based on some loose strings from the worm we tried to find out the payload. The worm searches Yahoo! Messenger application by searching window class named “YahooBuddyMain”, and then emulates keyboard events to send fake messages to all Yahoo! Messenger contacts.
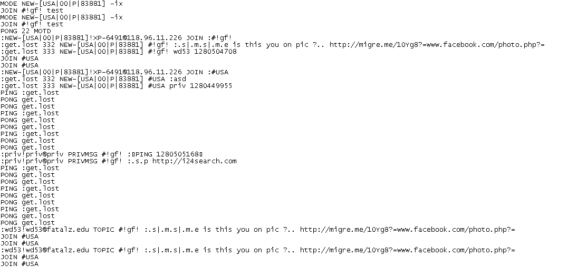
Incidentally the worm also tries to spread itself through IRC, below being an IRC log traffic event
Emsisoft Endpoint Protection: Award-Winning Security Made Simple
Experience effortless next-gen technology. Start Free TrialThe malware also monitors the keyboard strokes using GetKeyState and GetAsyncKeyState API, adding a possible keylogger activity.