Emsisoft Malware Spotlight: Blackbeard and Pigeon

 The independent IT security institute AV-TEST registers over 220,000 new malicious program signatures every single day.
The independent IT security institute AV-TEST registers over 220,000 new malicious program signatures every single day.
That’s a lot.
Many of these new programs are simply recombinations of older ones. Every so often, though, a new variant will come around that stands out from the crowd. This January, its name is Blackbeard and his sidekick Pigeon aka Zekos.
Downloader and Clickbot Defined
Blackbeard and Pigeon are a downloader and clickbot combo that began infecting computers around January 1st, 2014. A downloader is exactly what it sounds like: a program that is placed on your computer to download malicious content from the web. The Blackbeard downloader makes your computer download the malicious clickbot Pigeon. A clickbot is a program designed to turn your computer into a PPC ad clicking robot.
What’s PPC? Say you have a website, and it contains ads for other companies. In a Pay-Per-Click (PPC) advertising model, you would get paid a few cents by those other companies every time someone came to your site and clicked on one of their ads.
A clickbot takes advantage of the PPC ad model by a hijacking a computer and making it click on an ad a few thousand times. People who create clickbots use them to direct computers to ads on websites they own, so they can get paid.
Blackbeard and Pigeon Trojan Team
Downloaders and clickbots are nothing new. In fact, their combination is one of the most pervasive Trojans on the web today.
As a downloader, Blackbeard is effective because it is designed to run on both 32-bit and 64-bit versions of Windows. Most of the time, downloaders are just designed to run on one. In this sense, Blackbeard is a lot more “spreadable” than more traditional downloaders. Blackbeard can set virtually any type of Windows computer in operation today to download Pigeon. Like the legendary pirate it’s been named after, it’s an expert in hijacking.
Once Blackbeard “figures out” what type of operating system it’s on, it tells your computer to download Pigeon from a hardcoded website. Your computer will then store Pigeon as a randomly named, encrypted file in the Windows %SYSTEM32 directory. At this point, Blackbeard will also modify a Windows system file called rpcss.dll, to ensure the Pigeon module is loaded each time Windows starts and can perform its malicious activity.
Newer variants will also patch all cached copies of the rpcss.dll file present on a computer to make replacing the file and removing the infection more difficult.
SHA1 hashes of dropper:
95fe0ae549a228a3baa46e97eb37a4d013a74827
e458c21818be55bd94bbb49d96c56ce2e438e5d5
Blackbeard and Pigeon Symptoms
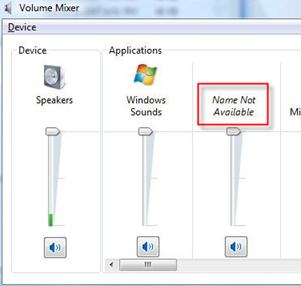
After downloading Pigeon, your computer will restart. A few more background process will occur, including additional malware downloads to ensure your computer will be turned into a clickbot. The key symptom to diagnosis has been audio ads running in the background of your computer and a “name not available” audio device under the audio devices tray icon in the Windows taskbar.
Additionally you may notice that svchost.exe is using a lot of CPU resources, which is caused by the click-bot component of the infection being active. It is good to note that the actual svchost.exe file is not involved in this infection and should be left alone.
Blackbeard/Pigeon Removal
If you think you’ve been infected by Blackbeard/Pigeon, turn your audio up to see if your computer is exhibiting the symptomatic “clickbot cough.” If it is, your computer is being used by someone else to make money on PPC ads.
To remove Blackbeard/Pigeon, you will need to go into your registry and replace the modified rpcss.dll file with a clean version. You’ll also need to delete the randomly named files that were created. Emsisoft Support can assist you with both of these tasks. They can also help you install a full version of Emsisoft Anti-Malware to help protect you from future threats like Blackbeard and Pigeon, and provide more technical information on this standout Trojan if you are interested.
Emsisoft Anti-Malware’s Behavior Blocker blocks this malware with an alert that a program is attempting to manipulate other processes. Please note, there are signs that this malware uses commonly exploited applications like Java, so it is very important to keep all installed software up to date.
Emsisoft Endpoint Protection: Award-Winning Security Made Simple
Experience effortless next-gen technology. Start Free TrialHave another great (malware-free) day!