Internet Zombie Defense Training, or: How Not to Become a Bot

Going on the Internet can be like walking through a post-apocalyptic city, where half the people you pass want to eat your brain.
In the post-apocalyptic city, these “people” are called zombies.
On the Internet, these zombies are infected computers, and we call them bots.
Bots and botnets are one of the most fundamental (and frightening) concepts of modern day malware. They are, very literally, networks of infection that allow their masters to hijack thousands of victims’ computing resources, to carry out any number of nefarious deeds or attacks over the Internet, for financial gain.
Don’t want to get bit? Then read below (and aim for the skull).
 Fact 1: A group of zombies is much scarier than just one
Fact 1: A group of zombies is much scarier than just one
Imagine going one-on-one with some undead ghoul. Do you hit it in the head, or just run away? Either way, you’re probably going to live to see another day. That’s how it works in the movies, at least. Individual zombies are pretty weak, but, in hordes, they are terrifying.
Strength in numbers applies to botnets as well. With botnet malware, the aim is to infect as many devices as possible. Once infected, devices become linked to a “Command and Control” server, which can issue remote commands.
 Fact 2: Zombies like brains
Fact 2: Zombies like brains
Botnet masters connect their victims to Command and Control servers because botnet masters like brains. The more brain, i.e. computing, power a botnet master has at their disposal, the better. This is because botnets are used to carry out coordinated attacks, which combine the computing resources of thousands of machines. Such attacks have one primary motive: to make money for the botnet master, or for a paying customer who has requested the botnet master’s criminal services.
 Fact 3: Zombies are evil
Fact 3: Zombies are evil
Like zombies, malicious botnets are pure evil. They exist solely to make money by wreaking havoc and destruction on everyone else.
Spambots hijack infected computers’ ability to email, as well as stored contact lists, to send out massive amounts of spam. Spam can be anything from annoying advertisements for sex products and diet pills, to malicious links and attachments that act as the “bite of the bot.” The increasing popularity of social media websites has now also attracted computing’s undead to places like Facebook and Twitter, where compromised profiles can be abused to spread comment spam.
Clickfraud botnets tell infected computers to go to a website and click on ads owned by the botnet master – or a client of the botnet master – making money for criminals AND slowing down your device by consuming RAM.
DDOS attacks tell thousands of infected bots to visit the same website at the exact same time, overloading the targeted site to the point of collapse. These “zombie swarms” are carried out to blackmail successful websites or to (illegally) take down the competition.
Bitcoin mining botnets such as Linkup can turn your PC into a mindless slave that dedicates its resources to creating various forms of cryptocurrency and making someone else rich.
Illegal material download or propagation can be carried out by bot computers without their owner’s knowledge or consent. In this scenario, the infected bot acts as a proxy, so that criminals can be criminals without having to leave evidence on their own device. Instead, the illegal activity – and potentially the blame – is shifted to you.
The ability to steal your financial information or identity usually comes included. “Command and control” means command and control, and, in addition to being used as a weapon, a bot computer can be told to share its stored information or its user’s activity with the botnet master, in numerous ways.
 Fact 4: Zombies don’t know that they’re zombies
Fact 4: Zombies don’t know that they’re zombies
And if you’re implicated in a botnet, you probably won’t know that your computer has become a bot. Your device will very literally be hijacked and told to perform malicious actions without your consent, behind the scenes.
 Fact 5: Zombies like to limp around and drool
Fact 5: Zombies like to limp around and drool
Nevertheless, one of the best ways to spot a zombie is its characteristic limp. If your computer becomes a bot, the situation will be much the same. An infected computer is most often a slow computer, as botnet masters’ primary objective is to steal the infecteds’ computing power. Accordingly, if your computer is acting slower than usual, you may be surfing with the undead. To find out, a simple CRTL + ALT + DELETE and a perusal of the Task Manager can be revealing, however bot detection is not always so simple. Most modern botnet masters make explicit efforts to counteract user detection. It is also important to note that even uninfected PCs carry out a number of important background tasks without explicit user consent, and that disabling these tasks in a fit of botnet paranoia can be just as disabling as actual infection!
 Fact 6: Zombies lurk in the shadows
Fact 6: Zombies lurk in the shadows
In most zombie-ridden after-worlds, you can spot members of the undead rotting and groaning from a mile away. This is not the case with botnets. Unlike zombies, botnets rely on deception, and they are typically propagated as Trojans or through social engineering. Botnet malware may deliver its payload through a malicious attachment disguised as something it’s not, or via a link to a fake website that surreptitiously initiates a “drive-by” download. Botnet masters may also disguise their creations as what appear to be useful apps – even security apps! – to get users to download and become part of their scheme.
 Fact 7: Once you get bitten by a zombie, you are not the same
Fact 7: Once you get bitten by a zombie, you are not the same
In many a zombie-flick, it often happens that one of the main characters gets bitten and infected. At this point, there is usually some (very brief) debate over whether or not the once-trusted comrade should be nixed. Typically, a cool headed hero will rise to action and do what needs to be done, much to the hysteria of his or her less rational team mates. “It needed to be done,” the hero will then explain. “He just wasn’t the same.”
With botnets, the situation is quite similar. You may know (and love) your PC or your mobile device with every beat of your digital heart, but once it becomes a bot it is no longer the same. The infected device will have a mind of its own, and it will no longer be that “trusted friend.” Any information you share with it will become accessible to the botnet master, and all that extra computing power you invested in will be consumed, as your device becomes a slave.
If you suspect your computer has become a bot- don’t wait. Contact our experts immediately, before the infection spreads. Zombie assassination is always free to anyone who requests it. Why? Because we like doing it.
 Fact 8: Zombies have one big weakness
Fact 8: Zombies have one big weakness
You’ve got to smash their brains.
With botnets, this doesn’t mean taking a hammer, a bat, a shotgun, or your post-apocalyptic weapon of choice to an infected device – but, it does mean getting inside the head of a botmaster. One need not understand the technical specifics of botnets proper to achieve a solid defense – just like no one really knows how zombies work, technically. For the average user, just knowing that botnets exist is almost enough on its own to avoid infection. From there, it is simply a matter of identifying the most common infection mediums…and not walking around the graveyard after dark.
Always use your brain – Whether it’s a website, an “urgent email,” or a personal messages sent through social media, always think before you click – otherwise your machine may be turned into a thoughtless, clicking machine! If you plan to download pirated software or media, you should also know that you will regularly be brushing shoulders with the undead.
Always take care of your weapons – Just like in the movies, it’s you against the somnambulant horde. The leaner, the faster, and the more efficient your weapons (i.e., software and applications) can be, the lower the odds you’ll get turned into a walker. Botnet masters specifically design their creations to exploit known weaknesses in popular software, so as to infect as many devices at once as possible. Avoiding infection is often as simple as enabling auto-updates on all of your main applications, and flat out discarding those programs you do not use so that you don’t have to worry about vulnerabilities. As an added benefit, this practice will increase the overall performance of your machine.
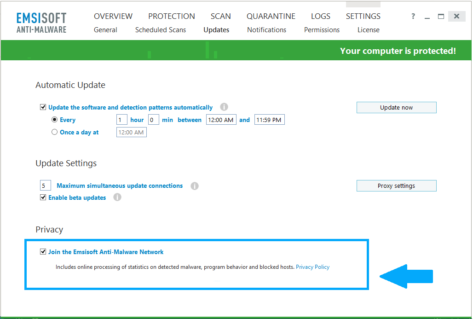
Always travel in a group – Fact #1 applies to the good guys too. Zombie slayers and botnet bruisers are strongest in groups. If you notice a strange background task operating on your PC, you should Google it and see what other people have to say. For specific files, you can also use Emsisoft’s isthisfilesafe.com. In addition, Emsisoft customers always have the option to become part of the Emsisoft Anti-Malware Network, a statistical service that allows Emsisoft to collect anonymous information from your machine, in order to identify botnet breeding grounds and sites where users are getting bitten.
To opt in, simply open Emsisoft, then click Settings > Updates > Join the Emsisoft Anti-Malware Network at any time.
Collected information always remains anonymous (see: Privacy Policy). Opting in can help thin the herd of Internet zombies and lead to more accurate detections by providing the Emsisoft Lab with actionable information.
Fact 9: Emsisoft Anti-Malware is like zombie body armor
Body armor: now there’s a concept too few zombie movies have used.
Imagine what that would be like – impenetrable suits of armor, completely immune to any zombie bite, worn by the entire human cast. Things wouldn’t be wouldn’t be so scary anymore. In fact, they’d be downright fun. Running from the zombies and just trying to survive would be more like ignoring the zombies or dreaming up new ways to make their heads go splat. Or, maybe even capturing zombies and training them to do all of humanity’s most mundane tasks, thereby rebuilding the post-apocalyptic world, better than it ever was before.
And botnets?
Well, we can’t condone actively hunting them (unless, of course, you know what you’re doing), but if you’re running Emsisoft consider yourself immune.
Emsisoft Enterprise Security + EDR
Robust and proven endpoint security solution for organizations of all sizes. Start free trialHave a great (zombie-free) day!