Strong indications that ransomware devs don’t like Emsisoft

As reported by our friends at Bleepingcomputer, the developers of the Radamant Ransomware Kit have now released a new, third version of their ransomware. This comes after the Emsisoft lab, led by our CTO Fabian Wosar, succesfully developed a decryptor for the previous two versions. The first version of Radamant encrypts data files with a RDM extension, while the second version uses a RRK extension. There are now rumors of a third version that we have not seen yet. For the first two versions, our developed decryptor can recover a victim’s files – for free. It comes to no surprise though, that the developer of the Radamant ransomware wasn’t very happy with Fabian and Emsisoft for interfering with his business.
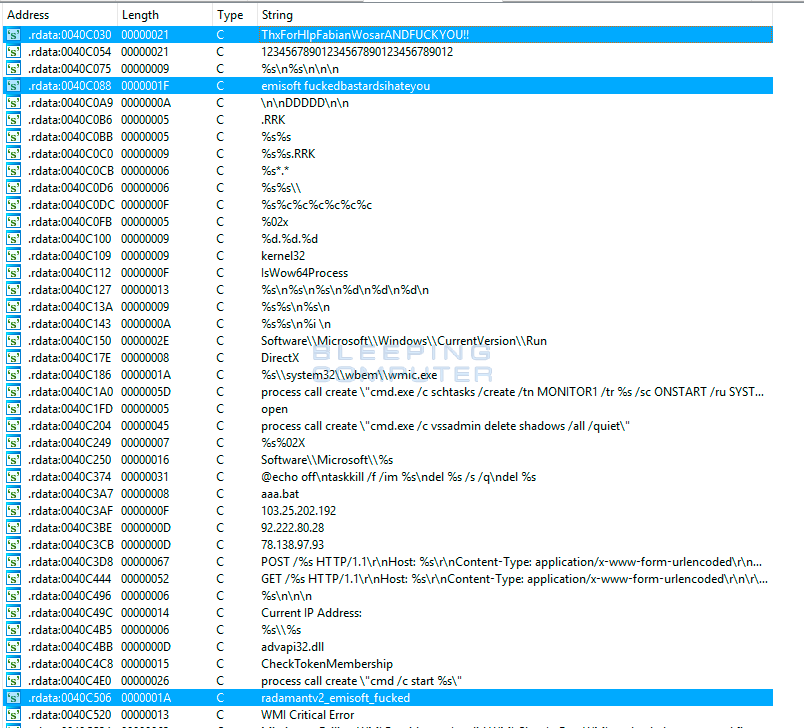
Take a look at the embedded strings in the ransomware malware executables and the domain names for their Command and Control Servers: For example, in the latest version of the malware executable there are strings such as emisoft f**kedbastardsihateyou that shows the developers displeasure that are really similar to “Emsisoft”. But see for yourself:
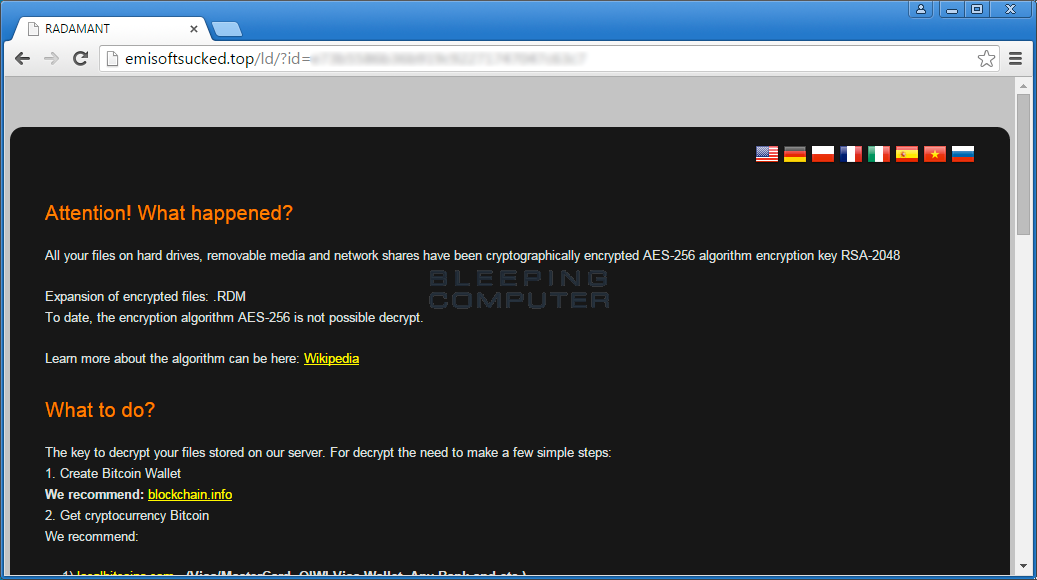
The Radamant developer also included Emsisoft in the domain name of one of his Command & Control servers: emisoftsucked.top (typo included).
As stated in this post, Fabian does not appear to be insulted, but rather quite the opposite:
“I am not really sure how things work in your circles, but in my circles getting insulted by malware authors is considered the highest kind of accolade someone can get, so thank you very much for that. Just next time, please try to get the company name right. But it’s a common mistake, so I let that one slide.”- Fabian Wosar
If you’re a victim of the Radamant ransomware and would like to recover your files and download our decrypter, please read and visit the forum thread at Bleepingcomputer in which you can find the most recent info and instructions.
Emsisoft Enterprise Security + EDR
Robust and proven endpoint security solution for organizations of all sizes. Start free trial Please note, that Emsisoft Anti-Malware running on the server won’t stop any infected clients from encrypting files on the shares. As of now, all variants can be successfully decrypted. We’ll keep you posted!
Please note, that Emsisoft Anti-Malware running on the server won’t stop any infected clients from encrypting files on the shares. As of now, all variants can be successfully decrypted. We’ll keep you posted!


