Emsisoft and Windows Firewall: Your questions, answered.

From (very) humble beginnings in a Windows XP Service Pack update, the Windows Firewall has evolved into a capable security tool. Today, its performance is on par with – if not better than – any modern third-party desktop firewall on the market.
In light of this, and after a lot of careful consideration, the Emsisoft team made a very conscious decision to rely on the Windows Firewall moving forward, which ultimately led to us merging Emsisoft Internet Security with Emsisoft Anti-Malware. This will allow us to concentrate our efforts on building a bulletproof product while using our Behavior Blocker technology to further strengthen the already rock-solid Windows Firewall.
To put it simply, using Windows Firewall in conjunction with Emsisoft Anti-Malware will provide better protection for our users, and that is our number one objective above all else.
Since our announcement of the Emsisoft Internet Security and Emsisoft Anti-Malware merger, we have received a lot of positive feedback. However, we also got a lot of questions. We want to take the time to answer the most frequently asked questions in a bit more detail:
So are you going to remove the firewall completely?
The answer to that question is not as simple as it may seem at first. Firewalls are usually divided into two parts: A so-called packet filter, which usually deals with incoming packets and is therefore often called an inbound firewall; and an application filter that deals with applications wanting to access the network or internet, which is why it is often also referred to as an outbound firewall. Emsisoft Anti-Malware has always had an application filter as part of its Behavior Blocker and that will continue to be true. The difference between the outbound firewall in Emsisoft Anti-Malware and Emsisoft Internet Security is that the former makes decisions autonomously, while the later, at least in theory, allowed you to also use your manual rules. In practice, the default for Emsisoft Internet Security was to automatically allow all outbound connections and the majority of all our users never changed it.
Why did you make the change? Was Emsisoft Internet Security less secure than the Windows Firewall?
No.
All firewalls on modern versions of Windows are based on the same technologies provided by Microsoft. In addition, inbound firewalls in particular are incredibly straightforward to implement, as they only block or allow access based on simple rules. That is why there is absolutely no difference in protection provided between any of the inbound firewalls on the market, including the Windows Firewall.
However, the Windows Firewall does have some benefits:
- Support for Windows Networking like Home Groups is a lot better in the Windows Firewall out of the box. There is no need to tweak any rules manually as was often the case for Emsisoft Internet Security.
- It is easier to use. This is mostly because third-party applications will take care of creating all necessary firewall rules for you. That is not an option that Emsisoft Internet Security could provide, as most software vendors don’t care about third-party firewalls.
- The Windows Firewall also provides much better compatibility. Third-party software vendors usually test their products with the Windows Firewall as it is part of Windows, but almost never test their product’s compatibility with aftermarket firewall products.
- Last but not least, the Windows Firewall also provides a lot more configuration possibilities to expert users and allows for much more complex rulesets than the inbound firewall offered as part of Emsisoft Internet Security.
But there are also a couple of disadvantages, which is where Emsisoft Anti-Malware 2017.8 comes in:
- Intelligent outbound firewall: The outbound firewall part of the Windows Firewall will by default allow every application to connect. This behaviour is actually identical with Emsisoft Internet Security, which also allowed any application to connect to the network or the internet unhindered by default. While both products can be manually configured to block programs from accessing the internet, most users don’t want to deal with this responsibility. This is where the intelligent outbound firewall that is part of our Behavior Blocker comes in, which will prevent malicious applications from communicating with the internet automatically while not getting in the way of benign applications.
- Enhanced malware protection: The Windows Firewall on its own does not provide any protection against more sophisticated attempts to bypass its outbound firewall through advanced techniques like code injection. Code injection essentially allows malware to take over a trusted program in order for its internet communication to pass through the firewall unhindered. Again, the Behavior Blocker in Emsisoft Anti-Malware is incredibly good at detecting and preventing these kinds of attacks.
- Windows Firewall Fortification: The functions Windows Firewall provides to software vendors to automatically create rules for their applications in the Windows Firewall for ease of use are also pretty much unprotected. That means that malware can and does create rules for itself automatically. In version 2017.8, we extended our Behavior Blocker technology to protect the exposed Windows Firewall functions from malicious usage. This gives you control over which of your applications are allowed to create Windows Firewall rules for you and which aren’t. This is what we refer to as “Windows Firewall Fortification”.
To sum things up, for inbound filtering, the Windows Firewall is just as solid a choice as any other firewall product on the market, including Emsisoft Internet Security. It provides better compatibility and is easier to use for the majority of users. Its drawbacks mostly revolve around its outbound filtering capabilities, which are perfectly complemented by the enhanced Behavior Blocker that is part of Emsisoft Anti-Malware 2017.8 and later.
Where can I find the new Windows Firewall Fortification options?
The new options are part of the Emsisoft Anti-Malware Behavior Blocker. As such, you can find them under Protection/Application Rules:
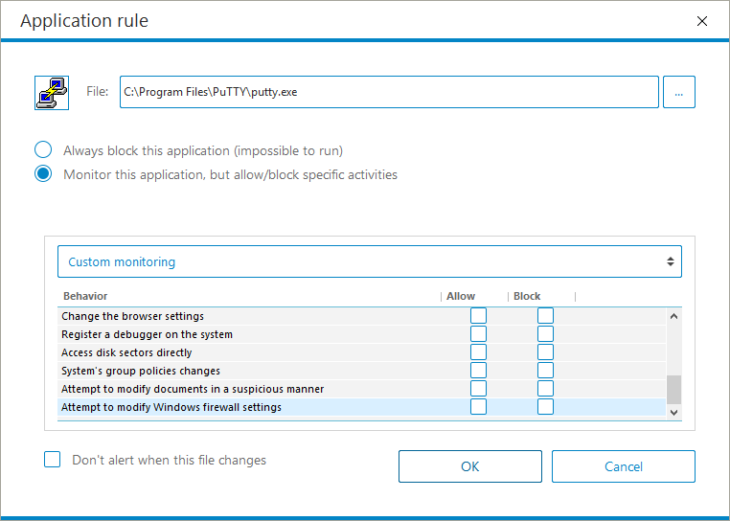
In addition, whenever the Behavior Blocker sees any application it doesn’t know to be trustworthy attempting to create new firewall rules or change the firewall status, it will attempt to auto-resolve the situation by blocking the attempt:
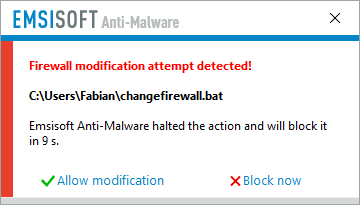
If you have auto-resolve disabled, it will simply ask.
Where can I find the “advanced configuration possibilities” you talk about? My Windows Firewall only has a couple of options!
The default dialog to configure the Windows Firewall can be incredibly deceptive at first. The advanced configuration dialog is stashed away behind an innocuous looking link in the normal Windows Firewall configuration dialog:
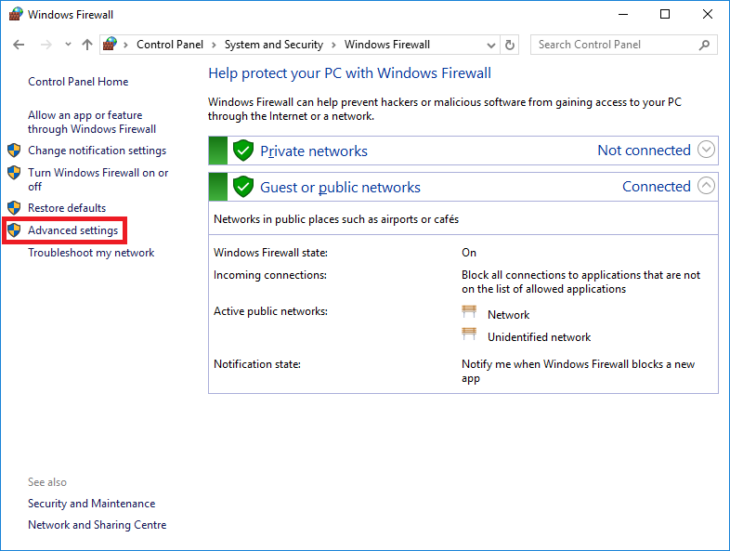
Windows Firewall dialog with link to Advanced settings
Clicking that link will expose the real configuration of the Windows Firewall where you have full access to all the rules it adheres by.
That looks awfully complicated. Are there easier methods?
There exist a slew of additional applications that sit on top of the Windows Firewall and attempt to enhance it by making rule creation and management easier. Some of the most popular are:
- TinyWall (Free) – http://tinywall.pados.hu/
- Windows Firewall Control (Freemium) – https://www.binisoft.org/wfc.php
- Glasswire (Paid) – https://www.glasswire.com/
That being said, we think that the majority of users probably won’t find these tools to be necessary. That is also why we decided against creating our own Windows Firewall front-end and focus our development efforts on improving the complementary and enhanced technology in our Behavior Blocker instead.
So what do you recommend I should do?
We strongly believe that the combination of Emsisoft Anti-Malware and the Windows Firewall is the best option for almost every user. For the past 12 years while developing our product, we used this exact combination in all of our internal performance evaluations of our technology. Our malware research team works hard to make sure that even the most advanced threats are blocked immediately across all our products.
So yes, Emsisoft Anti-Malware blocks the same malware that Emsisoft Internet Security blocks out of the box – no configuration, paying extra or jumping through hoops needed.
If you do feel the need to make sure that certain legitimate applications can’t access the internet, the Windows Firewall does offer the ability to do so via its Advanced Settings. If you find that method to be too inconvenient, going with one of the many front-ends may be an option for you.
We do know that a small minority of Emsisoft Internet Security users believe that the Windows Firewall must have backdoors implemented by Microsoft to allow them to spy on their users. In all our research, we haven’t found one and neither have hundreds of other security professionals that constantly review Windows for possible backdoors and vulnerabilities.
We also think it is important to keep in mind that every single firewall product for Windows Vista and later uses the very same frameworks to implement packet and application filtering. There is no difference between the Windows Firewall, Emsisoft Internet Security and any other third party firewall from a technical point of view. If Microsoft were to backdoor their products to allow unhindered communication, this backdoor would probably be part of the Windows Filter Platform or the NDIS Lightweight Filter Framework, which are the underlying technologies all firewall products are built upon, and affect every firewall product equally.
If you still prefer to use a firewall product other than the Windows Firewall, we recommend you contact the software company creating your new firewall product of choice beforehand to ask them whether they implement their own firewall or rely on the Windows Firewall as well. Most firewalls and internet security suites dropped their own implementation in favour of the Windows Firewall many years ago. So we suggest you ask them first to make sure you don’t end up with a Windows Firewall front-end instead.
Do you have more questions? Post them in the comments and we’ll answer them.
Emsisoft Endpoint Protection: Award-Winning Security Made Simple
Experience effortless next-gen technology. Start Free TrialHave an excellent (malware-free) day!


