Ransomware-as-a-Service: Commoditizing ransomware

One of the most profound changes in the modern business landscape has been the gradual shift to the Subscription Economy. In years gone by, you handed over your hard-earned money and in return received a product or service that was yours to keep. Now, both companies and consumers are ditching the traditional pay-per-product approach in favor of the as-a-service model – an arrangement that offers greater flexibility for consumers and more predictable, stable income for businesses. In most cases, it’s a better all-round experience for everyone involved.
Sadly, it’s not just Netflix and Spotify that have adopted this way of offering their services. In the dark recesses of the digital underworld, malware authors hawk ransomware subscriptions that are swiftly snapped up by buyers with unscrupulous motives. A relatively recent phenomenon, Ransomware as a Service (RaaS) allows anyone with an internet connection – regardless of their technical literacy – to purchase powerful ransomware via the Dark Web and carry out devastating encryption attacks against the targets of their choice.
How does Ransomware-as-a-Service work?
Ransomware itself is a special type of malware that is designed to encrypt your files and render them inaccessible until you fork over a sum of cash (usually in the form of bitcoin or another cryptocurrency). You can get further insight into how ransomware works in our previous blog post here.
In the past, only those with strong technical chops could execute a successful ransomware attack, but Ransomware-as-a-Service has changed all that thanks to the proliferation of user-friendly ransomware kits, which contain everything one might need to launch a successful ransomware attack.
These kits are typically hosted on portals buried deep in the Dark Web, where buyers can “safely” deploy the ransomware away from prying eyes. Many RaaS kits require no upfront cost to use or deploy; instead, the author receives a commission (typically 20-40 percent) of any illegal earnings, making RaaS – for all intents and purposes – an affiliate scheme. This makes it a lucrative business model for buyers and ransomware authors alike, as both parties are able to cash in on the ransomware on an ongoing basis.
After gaining access to a RaaS kit, buyers then need to distribute it either independently or via a paid service. Attack vectors can take many forms, with phishing being one of the most common methods due to how readily unsuspecting users will click on foreign links and execute unfamiliar programs.
Alternatively, RaaS kit buyers may seek out systems with unguarded remote desktop protocol by purchasing a list of vulnerable machines or scanning the internet for them using widely available tools. The RaaS process might look something like this:
- Malware author(s) create a RaaS kit for a cybercrime group.
- The group promotes the RaaS kit on the Dark Web and other platforms.
- Buyer purchases the RaaS kit.
- The buyer distributes the ransomware either on their own or with the help of a dedicated distribution service.
- If successful, the targets are infected!
Examples of infamous Ransomware-as-a-Service
Satan
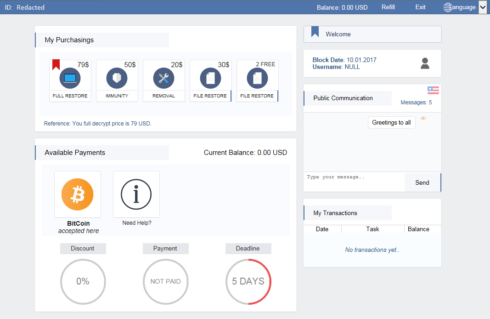
First spotted in early 2017, Satan RaaS allows affiliates to effortlessly create and deploy their own ransomware in a matter of minutes. Satan RaaS is free to use, but ransomware authors receive a 30 percent cut of any ill-gotten gains. Satan RaaS is particularly notable for its ease of use, professional-looking GUI that features simple customization options, handy distribution tips and even a metrics dashboard where users can keep track of infection rates, ransom generated and more.
Philadelphia
Philadelphia bucks the subscription model and instead can be purchased outright with a one-time upfront cost of $389. As far as commercial ransomware goes, this is definitely on the more expensive side of things, but the developers of Philadelphia justify it by providing a professional feature set that rivals most legitimate software. Buyers of Philadelphia gain access to an intuitive interface, lifetime access, the ability to generate unlimited ransomware samples and ongoing support and updates.
Cerber
Distributed through an underground Russian forum, Cerber is one of the most infamous examples of RaaS to date. In June 2016, an early iteration of Cerber caused massive headaches for Microsoft when millions of Office 365 users were exposed to the ransomware. Later, in September 2017, it was found that a U.S. government website was hosting a JavaScript downloader that delivered Cerber. Unlike some ransomware, Cerber doesn’t rely on network communication to function, meaning even offline machines that have been infected are at risk of having their files encrypted.
MacRansom
MacRansom puts to rest the lingering rumor that MacOS is somehow invulnerable to malware. In June 2017, researchers spotted portals on the Dark Web selling MacRansom, ransomware that – unlike the vast majority of ransomware – specifically targets Mac OS users. Affiliates keep a 30 percent cut of any ransoms generated, with the rest going to the ransomware authors. Interestingly, MacRansom is quite primitive compared to many Windows ransomware variants and requires a lot of manual input from the author, making it far less efficient than other RaaS.
The rise of Ransomware-as-a-Service
It’s no secret that ransomware attacks have exploded in popularity in recent times. In fact, as SonicWall reported, the number of ransomware attacks increased an astonishing 167 times over the course of a single year, rising from 3.8 million in 2015 to 638 million in 2016.
The growing availability of RaaS is largely to blame for this alarming trend. Fuelled by the sheer profit potential, 2016 saw the birth of almost a quarter of a million new ransomware variants, which helped cybercriminals generate about $1 billion through the use of ransomware. Meanwhile, the average ransomware demand more than tripled, rising from $294 in 2015 to $1,077 in 2016.
As the ransoms have grown larger, so too have the expectations of RaaS affiliates. While the ransomware of yesteryear was technically challenging to deploy for the average person, RaaS has become steadily more accessible and user friendly to meet the needs of criminals who may not be technologically inclined. Spurred on by ransomware such as Spora, whose interface and functionality resembles that of professional software, some modern RaaS is beautifully designed, intuitive to use and even features handy help guides.
The way RaaS is marketed has also become more advanced. Once confined to the Dark Web, malware groups are getting increasingly brazen when it comes to marketing tactics and have begun encroaching on the Surface Web (the part of the internet that regular users inhabit).
For example, part of Philadelphia’s promotional campaign included a high-quality YouTube introductory video highlighting all the ransomware’s features and how new users can get started. Similarly, the author(s) of Karmen released a short instructional YouTube video showing the ransomware in action. See it for yourself in the following YouTube video from Recorded Future, who rehosted the video and removed the links to the ransomware.
What are the risks for businesses?
Businesses of all sizes face an ever greater risk as RaaS becomes more accessible, but it’s not the ransom itself that’s the killer – it’s the downtime. About 1 in 6 ransomware infections result in more than 25 hours of downtime, according to figures collated in a recent industry report, with some organizations reporting disruption lasting in excess of 100 hours. Unable to make sales, provide support or talk to prospects, it’s easy to see how RaaS can indirectly cost small- and medium-sized businesses tens of thousands of dollars in lost revenue.
Because RaaS attacks are commonly used to target specific companies or industries in order to maximize profits, some sectors are innately at far greater risk than others. In fact, according to research from Dimension Data, four industries account for 77 percent of all ransomware attacks:
- Business and Professional Services (28%)
- Government (19%)
- Healthcare (15%)
- Retail (23%)
If you operate in one of these sectors, it’s vital that you’re extra vigilant in order to minimize the risk of becoming a victim of a RaaS attack.
How to protect your company from ransomware attacks
As with all types of malware, when fortifying your system against attacks by one of the many ransomware as a service affiliates, it’s wise to take a multipronged approach, including:
Backups
Taking a proactive approach to RaaS is a good way to minimize the risk of infection, but for the ultimate peace of mind you need to know you can quickly restore your system in the event of an attack.
That’s where backups come in.
Both cloud and physical storage are very affordable these days, meaning there really is no excuse to not be making regular backups. For the ultimate peace of mind, we recommend abiding by the 3-2-1 rule:
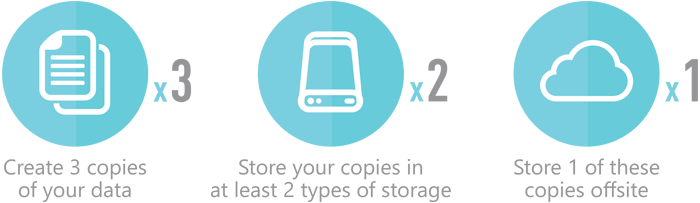
Keep at least three copies of data on at least two different types of storage, at least one of which must be stored off premises. In a perfect world, all these copies would be identical and updated regularly (in real time, ideally).
Employee training
Accounting for almost 3 in 4 of all malware attacks, phishing is an incredibly popular attack vector and RaaS is no exception. With this in mind, one of the most critical things you can do to protect your organization from RaaS is bring all your employees up to speed on best safety practices to use when browsing the web and checking their emails.
Giving staff the support they need to learn how to identify suspicious messages and encouraging them to avoid potentially dangerous links and email attachments can go a long way toward reducing your risk of a RaaS infection.
You can find an extensive range of tutorials and how to’s on our blog, including our excellent anti-phishing guide!
Antivirus that uses behavioral blocking
New RaaS variants are being released at such a fast rate that it’s simply not possible for antivirus products that rely solely on a signature database to catch them all. As such, it’s important to use IT security software that incorporates behavioral blocking technology into its defense mechanisms.
By keeping an eye on your system and watching for suspicious behavior that may be caused by malicious software, Emsisoft Anti-Malware is able to identify all types of ransomware and put a stop to the guilty program before it can even lay a finger on your files.
Ransomware services are here to stay
The subscription economy has ushered in a new era of convenience and flexibility – and ransomware. As RaaS becomes more accessible, even the least technically minded criminals have the means to deploy targeted ransomware attacks on organizations and consumers around the world. Nevertheless, by staying proactive and using best security and backup practices, you can maximize your chances of keeping your business safe.
Emsisoft Endpoint Protection: Award-Winning Security Made Simple
Experience effortless next-gen technology. Start Free TrialHave a great (ransomware-free) day!