New Ransomware Alert: CryptoLocker copycat PClock discovered

Ransomware CryptoLocker was one of the most infamous malware families of the years 2013 and 2014 and although the operation behind the original CryptoLocker malware family has been dismantled in 2014, it’s still a name that frightens a lot of users and system administrators alike. It is therefore not surprising that other malware authors try to capitalize on CryptoLocker’s reputation by releasing copycats. One of the most recent copycats that we became aware of is a ransomware named PClock that showed up just a day ago. Unlike CryptoLocker though, which was a somewhat complex and sophisticated piece of malware, PClock is quite primitive by nature.
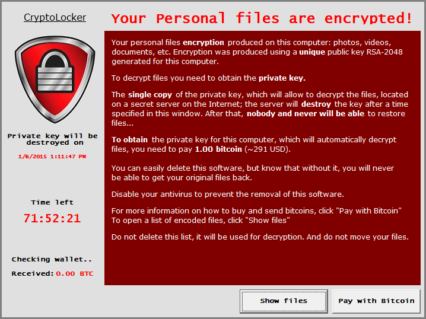
72-hour countdown timer to pay USD$300 ransom
Like all file encrypting ransomware (also known as crypto malware) PClock’s main goal is to encrypt important files on the victim’s system in order to compel them to pay a ransom in return for their files. Like CryptoLocker it gives the user a 72-hour ultimatum to pay the ransom of 1 bitcoin (approximately USD $300). Otherwise it claims to destroy the keys required to decrypt the user’s files:
If a user does not pay the ransom within the allotted time, it will display a last_chance.txt file that tells the user to download the malware again, which supposedly gives you another 3 days to make the payment. In reality though PClock does not destroy any keys, so the countdown is pretty much meaningless.
How PClock infects a new system
At this point it is not entirely clear how PClock, which is written in Visual Basic 6, enters a user’s system. Once it manages to to execute on the victim’s system however, it will copy itself to the current user’s application data folder using the sub-folder “WinCL” and the file name “WinCL.exe”. It then establishes persistence by creating a new registry value within the HKEY_CURRENT_USERSoftwareMicrosoftWindowsCurrentVersionRun key named “wincl” pointing towards the newly created WinCL.exe executable. The malware then tries to encrypt the victims’s files. It specifically targets files with one of the following extensions:
*.3fr, *.accdb, *.ai, *.arw, *.bay, *.cdr, *.cer, *.cr2, *.crt, *.crw, *.h, *.dbf, *.dcr, *.der, *.dng, *.doc, *.docm, *.docx, *.dwg, *.dxf, *.dxg, *.eps, *.erf, *.indd, *.jpe, *.jpg, *.kdc, *.mdb, *.mdf, *.mef, *.mrw, *.nef, *.nrw, *.odb, *.odm, *.odp, *.ods, *.odt, *.orf, *.p12, *.p7b, *.p7c, *.pdd, *.pef, *.pem, *.pfx, *.ppt, *.pptm, *.pptx, *.psd, *.pst, *.ptx, *.r3d, *.raf, *.raw, *.rtf, *.rw2, *.rwl, *.srf, *.srw, *.wb2, *.wpd, *.wps, *.xlk, *.xls, *.xlsb, *.xlsm, *.xlsx
Every files the malware tries to encrypt is recorded within a file named “enc_files.txt” located in the victim’s profile folder. After the encryption has finished the malware will try to delete and disable all shadow copies. Shadow copies is the technology that powers the Windows’ “Previous Version” feature that allows a user to restore previous versions of a file. This feature is often used by ransomware victims to recover their files so a lot of ransomware families started to destroy any previous versions created by the shadow copy service. Last but not least the malware will create a shortcut to itself on the victims’s desktop and change the victims’s desktop wallpapter to the following picture:
During the infection and encryption process the malware will try to maintain a log on the malware author’s command and control server:
P04552 8:08:02 AM Files encrypted
P04552 8:08:02 AM STATE: CRYPTED_OK
P04552 8:08:02 AM Delete shadows
P04552 8:08:04 AM Shadows: no ADMIN
P04552 8:11:06 AM Shadows deleted
P04552 8:11:06 AM STATE: SHADOWS_OK
P04552 8:11:06 AM Prepare
P04552 8:11:08 AM Saved BTC price – 330
P04552 8:11:11 AM Shortcut created
P04552 8:11:12 AM STATE: PREPARE_OK
P04552 8:11:12 AM Change wallpaper
P04552 8:11:13 AM Wallpaper changed
This excerpt shows an example of an infection taking place to give you an idea about what is being logged.
PClock: a lot of show but little substance
Similar to the countdown, the ransom note is far from the truth as well and even though the malware may look somewhat professional at first glance it becomes obvious quickly that the people behind it are amateurs at best. The encryption algorithm used for example is just a simple XOR based obfuscation that uses a constant key on all systems. Due to that we are able to provide a decrypter that can be found further down this post. A more severe sign for the lack of professionalism is the fact that the malware contains several disastrous bugs that may cause data loss on the victim’s system. If the malware encounters a particularly large file for example that is too big to fit into memory the malware will end up truncating the existing file instead of encrypting it. The result is a 0-byte file that contains neither the original nor the encrypted file content. Once the malware messed up a file like that the last hope for the victim are data recovery tools.
How to unlock your encrypted files
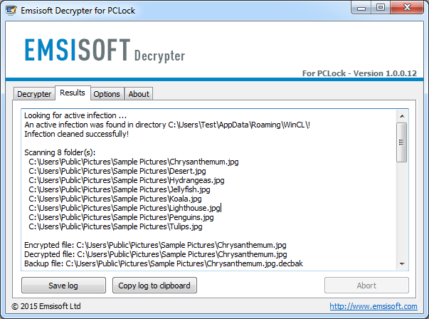
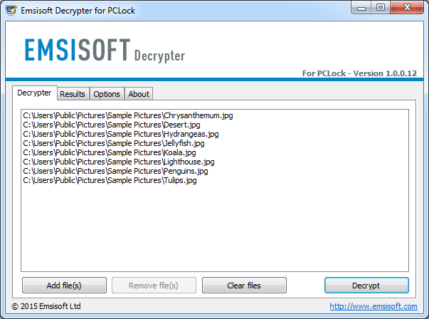
As mentioned before the encryption used by PClock is extremely weak and can easily be reverted. To help and guide you in that process we developed a small decrypter utility. Our decrypter will enable you to decrypt any PClock encrypted files that haven’t been damaged beyond repair by the malware and clean up your computer without having to pay the ransom. You can download our decrypter here: http://emsi.at/DecryptPClock
The decrypter will use a list of encrypted files the malware stores on the victim’s system to determine which files are in need of decryption. This list is loaded automatically when you start the decrypter and in theory all you would have to do is load up the decrypter and hit the “Decrypt” button. In practice it isn’t that simple though due to the fact that the malware does not provide enough information for the decrypter to be absolutely sure that the decrypted file is exactly like the original unencrypted one that the malware targetted. We therefore decided to play it safe and keep backups of all encrypted files. These backups will take a lot of disk space and essentially double the amount of space required on your hard disk to hold both the decrypted file as well as the encrypted backup. If you are running low on disk space you can disable the backups in the decrypter’s option menu. This should be a last resort though and before you try to use the decrypter that way you should try the decrypter out on a small number of test files that you can verify manually to make sure the decrypter is operating correctly.
If you don’t feel comfortable performing the decryption process on your own, feel free to create a support request in our support forum or send us an email.
UPDATE 2015-01-06, 8PM UTC: An updated version of PClock was released where this decrypter does not work with yet. We’re working on an update. Please return in a couple of hours if you are affected by the threat. Please also read this thread at the Bleepingcomputer forum where this topic is discussed.
UPDATE 2015-01-09: the malware authors released two more versions of PClock. The good news is that the Emsisoft decrypter is ready and works for both versions. You can download the Emsisoft decrypter version 2 here. Read the instructions thoroughly first on page 8 in the Bleepingcomputer forum discussion.
UPDATE 2015-01-10: new decrypter developed, download here: http://emsi.at/DecryptPClock2. Please read the Bleepingcomputer discussion thoroughly for instructions.
NOTE: Emsisoft’s Fabian developed this decrypter in his spare time for victims of PClock. If you’re a victim, please read the instructions entirely before starting the process. To prevent getting infected in the first place, use Emsisoft Anti-Malware for complete protection against ransomware, viruses and all other sorts of malware. We’d appreciate it if you share this post so that more victims of PClock can be helped.
Emsisoft Endpoint Protection: Award-Winning Security Made Simple
Experience effortless next-gen technology. Start Free TrialHave a great (ransom-free) day!