Exploit kit attacks DNS settings of over 50 different router models

Internet users that have not secured their wireless router may soon face potential issues. A French researcher has discovered an exploit kit that targets and attacks many well known router models from reputable manufacturers.
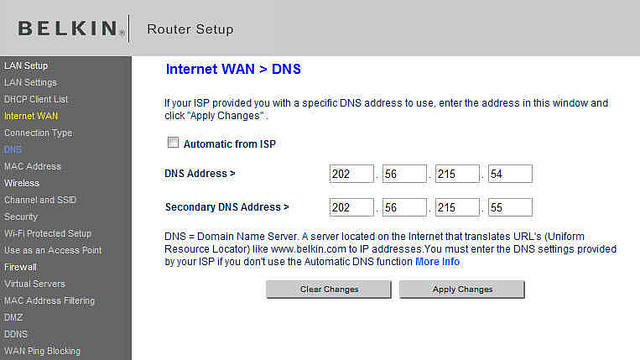
In recent times, home and office routers (SOHO) have become a primary target for hackers that are seeking to redirect web traffic to malicious websites. In this specific case, hackers are now using a complex exploit kit on your router DNS settings in order to carry out cross-site request forgery attacks.
A French researcher named Kafeine has discovered an exploit kit and published research about the attacks on Friday. Kafeine said that at the attacks peak on May 9, after a month long series of modifications from attackers including JavaScript obfuscations that the traffic from the campaign peaked at approximately a million hits.
Traffic redirection results from hijacked router DNS settings
Particularly, the attackers are driving a lot of web traffic from Chrome users. Such an occurrence is an example of a pharming attack and is considered to be dangerous because it puts online banking and sensitive transactions/communications at risk.
Kafeine stated:
“This kind of attack is really old, but that this is the first time that I’ve seen something with obfuscation, rotating domains and landing going after DNS.”
Office and home routers are infected in this malicious campaign via drive by downloads and malvertising. The attackers concentrate on Chrome and Chromium based users possibly because of their ability to discover local and public IP addresses by using tools such as WebRTC-ips. WebRTC-ips is present in popular web browsers such as Chrome and Firefox and allows browsers and mobile apps to communicate in realtime via API’s.
CSRF attacks force victims to submit malicious requests on behalf of a hacker, typically on sites where a victim is already logged in. Kafeine stated the original exploit code was written in the clear, but within a month had added obfuscation and many other improvements. There is a long list of routers vulnerable to this type of attack including D-Link, Belkin, Netgear, Asus, and others.
Kafeine wrote:
“In the attack, the DNS address was changed to 185[.]82[.]216[.]86; it has since been changed to 217[.]12[.]202[.93], and always uses Google’s DNS as a failover should the first IP fail.”
Update your router firmware
Users are at risk of financial loss, click-fraud, man-in-the-middle attacks, and even phishing. It is recommended that everyone updates their router firmware and software and secure their router using strong password and security settings.
Emsisoft Enterprise Security + EDR
Robust and proven endpoint security solution for organizations of all sizes. Start free trialHave a great (CSRF-free) day!