Seasonal ransomware highlights the need for better reporting and information sharing

In 2019, there has been an unprecedented number of ransomware attacks on governments, schools, school districts and healthcare organizations in the U.S., with more than 621 entities being impacted in the first nine months of the year (see State of Ransomware in the U.S.: 2019 Report for Q1 to Q3).
The rate of attacks has, however, slowed in recent weeks. In July, 44 organizations were impacted; in August, 24; in September 24 again; and in October, only 16. We initially speculated that the decrease was due to U.S. organizations being on high alert, bolstering their IT and, as a result, being less susceptible to attack. Given the deficiencies in public sector security that were highlighted by the research of UMBC’s Professor Donald Norris and his team and by the damning report issued last month by the Mississippi Department of Audit, it would seem that improvements are much needed, so this would have been good news indeed.
It appears, however, that we may have been mistaken about the reason for the decrease. Data collected by the EPSRC EMPHASIS Ransomware project and shared with us by Professor David Wall of the University of Leeds shows mid-year spikes in previous years too.
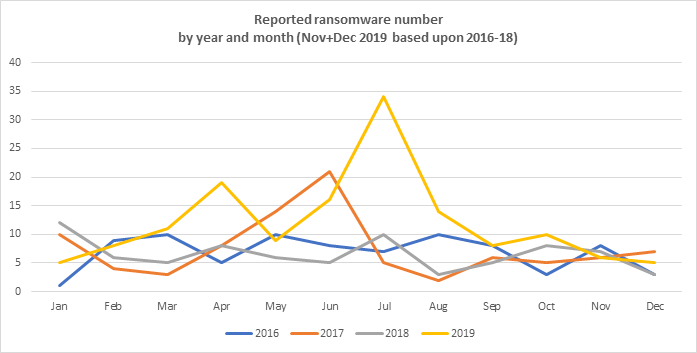
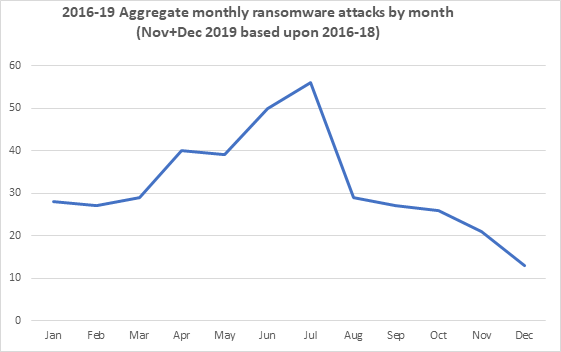
Why would this be? Professor Wall believes it may be due to threat actors timing attacks for the periods in which organizations are likely to be most vulnerable. “Our interviewees told us that attackers tended to launch campaigns when organizations were ‘off guard’ and weaker, such as at holiday times, when they were undermanned and covered by less skilled workers, so the attacks are more successful,” said Wall.
Another possibility is that the rate of attacks is constant, but attacks are more likely to succeed during vacation periods for the reasons Professor Wall stated. Other factors may be at play too. For example, it could be the case that employees will be familiar with types of email they typically receive, so are likely to be able to spot a message that is unusual and potentially malicious. They may not, however, be so familiar with the types of emails their colleagues receive so, when covering during vacation periods, may be more likely to open a malicious attachment – especially as they will be busier than usual.
This is simply speculation, of course, and, without additional data, it is impossible to say with any certainty why ransomware attacks spike at certain times of year.
This does, however, highlight the need for better reporting of security incidents. If organizations understand when and why they are most susceptible to attack, they can take steps to mitigate the risk.
Currently, relatively little data available. Private companies often choose to make no public disclosure in order to protect their reputations while public entities often release only very limited information. The type of ransomware involved, the attack vector, the vulnerability that was exploited, the amount of the ransom demand, whether it was paid and the financial impact of incidents are very often not known.
Were such information to be centrally reported, it could be aggregated, anonymized and shared with academics, security researchers and other organizations. This would provide a much clearer picture of the threat landscape, enable actionable intelligence to be created and shared and for organizations to better assess their security priorities.
As Marc Barrachin and Algirde Pipikaite recently stated in an article for Harvard Business Review, “Information is power and, in cybersecurity, it’s the power to prevent other similar events.”
Emsisoft Endpoint Protection: Award-Winning Security Made Simple
Experience effortless next-gen technology. Start Free TrialNote: EPSRC EMPHASIS Ransomware Project’s statistics may not match our previously released statistics as the data sets are yet to be aggregated. The EMPHASIS Ransomware Project is a cross-disciplinary research project across six universities that is exploring why ransomware is so effective as a crime and why are so many people falling victim to it?


