HelloKitty ransomware group likely responsible for CD Projekt attack. Here’s why.

A few days ago CD Projekt, the Polish video game company behind Cyberpunk 2077 and The Witcher, revealed that it had been hit by a ransomware attack.
Overview
On 9 February 2021, CD Projekt confirmed via Twitter that an unidentified actor had gained access to their internal network, encrypted some devices on the network and stolen data.
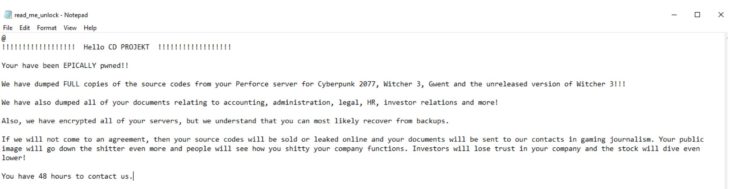
In their ransom note, threat actors claimed to have stolen full copies of the source code for Cyberpunk 2077, The Witcher 3, Gwent and an unreleased version of The Witcher 3, along with documents relating to accounting, administration, legal, HR, investor relations and more.
The attackers threatened to sell or leak the stolen source code online and send the stolen documents to journalists in the gaming industry if CD Projekt refuses to cooperate.
CD Projekt believes that no personal user or player data was stolen during the incident.
CD Projekt refuses to negotiate with attackers
In response, CD Projekt stated that it does not plan to negotiate with the attackers and is already taking steps to restore the affected data from backups and work with any parties that may be affected by the breach. The company is also working with law enforcement and IT forensic specialists to fully investigate the incident.
We wholeheartedly support CD Projekt’s decision to not pay the ransom. Paying the ransom doesn’t always lead to the safe decryption of encrypted data, nor does it guarantee that the criminals won’t just leak the stolen data anyway. On a more macro level, paying ransom money incentivizes further attacks and fuels the ransomware cycle, and may be used to fund other serious criminal activity.
Since the incident, we have seen a user auctioning what appears to be the stolen source codes of Cyberpunk 2077 and The Witcher 3 on an underground forum. The auction starts at $1 million. 28 GB of data corresponding to the source code for Gwent has been confirmed to be leaked, originally the leak was posted on the file-sharing site MEGA
Update 2/12/21: The auction has closed. The hackers allegedly sold the stolen data to a buyer from outside the forum on the condition that the data not be distributed to any other parties. It is not clear who the buyer is or how much the data was sold for. The auction’s opening bid was set at $1 million with a buyout offer of $7 million. The fact that the auction has closed suggests that the buyer was willing to pay at least $7 million for the data, but what they intend to do with the stolen source code remains a mystery.
There is another possible scenario that we think is more likely: no buyer exists and the closure of the auction is simply a means for the criminals to save face after failing to monetize the attack following CD Projekt’s refusal to pay the ransom. We have seen this behavior in the past with REvil, a ransomware group that threatened to release damaging information about Donald Trump. Although the hacked law firm refused to pay to prevent the leak, the information was never published – the attackers just claimed to have sold it.
Provisional Technical Analysis
While CD Projekt has been admirably transparent about the incident, the company has shared few details regarding who is responsible for the attack.
Based on the naming conventions of the ransom note, we believe that the ransomware used in the attack was HelloKitty. The ransom note posted by CD Projekt is named “read_me_unlock.txt” and HelloKitty is the only ransomware we’ve observed that uses that naming format. In addition, the language used in the ransom note is similar to that we’ve seen in other HelloKitty ransom notes.
First observed in early November 2020 by security research MalwareHunterTeam, HelloKitty is a little-known ransomware variant that has targeted a handful of large companies, including Brazilian power company CEMIG. Victims are instructed to communicate with HelloKitty operators through email or deep web .onion websites.
HelloKitty gets its name from a mutex named ‘HelloKittyMutex’ that is used when the ransomware is executed. A mutex allows all processes to use the same resource, but not simultaneously; in the case of HelloKitty, HelloKittyMutex prevents the ransomware from running more than one instance of itself at a time.
When executed, HelloKitty terminates 1,706 processes, shuts down 57 services and deletes shadow copies via Windows Management Instrumentation.
Because there are multiple versions of HelloKitty, it’s impossible to say which encryption method was used in the Projekt Red attack without seeing a sample. We have seen versions that use AES-256 + RSA-2048 encryption, others that use AES-128 + NTRU and a Linux version that uses AES-256 + ECDH.
Note: Some analysts may refer to HelloKitty as DeathRansom, a strain of malware that was originally only capable of renaming files. Different versions of DeathRansom were later developed that could encrypt files in various ways. However, the relationship between DeathRansom and HelloKitty is still not fully clear.
What happens next?
The full impact of the incident remains to be seen. From a business perspective, the attack could diminish the company’s reputation, which has already been battered following the bug-ridden launch of Cyberpunk 2077. From a security perspective, cyber criminals could use the leaked source code to scour for vulnerabilities in CD Projekt’s products, which could potentially impact users.
We will update this article over the coming days as we analyze the available samples and more information becomes available.
Emsisoft Enterprise Security + EDR
Robust and proven endpoint security solution for organizations of all sizes. Start free trial