World of Warcraft Expansion Pack Phishing Scam

 Gamers Beware!
Gamers Beware!
There’s a new email phishing scam going around, and it specifically targets World of Warcraft players anxiously awaiting the upcoming release of The Warlords of Draenor expansion pack.
Unlike earlier phish attempts that dangle invites to test the expansion pack’s beta, this latest scam promises free skill upgrades and gold, which players can pre-install with a complimentary Game Key and which will apparently be activated upon The Warlords of Draenor expansion pack release.
Like many a phish, the email also includes a link to a malicious website. In this case, the website is a mock-up of Blizzard’s official Battle.net log-in page that uses the same design as the real one. The pretense of this phish is that players must log-on to cash in on their complimentary Game Key and all of its cool gifts, but in reality log-in credentials are sent to the scammer. With username and password in hand, scammers can then log on to their victims’ actual accounts to glean personal and financial information.
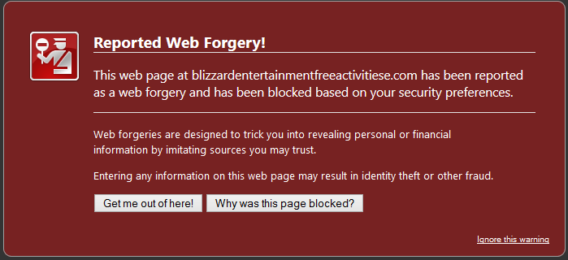
Reports have indicated that one website involved in this scam is located at blizzardentertainmentfreeactivitiese.com. Fortunately, major browsers such as Chrome and Firefox have already flagged the site as malicious.
Dealing with Unsolicited Offers and Requests
The highly targeted nature of this latest attack suggests that the person behind it is most likely a World of Warcraft player, or at least someone with a working knowledge of the game. Language in the phishing email makes mention of specific items and skills from the game, and even imposes restrictions that only someone familiar with game play would know of. Such an appeal to insider knowledge is a common phishing technique. This particular attack also imposes a deadline to cash in on the offer, a clear attempt to get people – who are already excited about the expansion pack’s release – to act before they think.
Unsolicited emails are one of most common cybercrime vectors in use today. In a large majority of cases, attacks come in the form of non-targeted spam designed to make money through pay-per-click advertising schemes; but, spam can also be used to propagate malware. Fortunately by now, most of us know spam when we see it, or for that matter simply don’t see it at all because email services have gotten so good at blocking it – but targeted phishing emails aren’t always so easy to spot.
A targeted phish takes time and effort. It requires research on the targets, construction of a convincing landing page, and most importantly a cleverly deceptive email. All of this takes time and more importantly money, which means that in all but the most advanced and determined campaigns, some element of the phish will have a flaw. Cybercriminals are financially motivated beings, and most choose a quantity over quality approach even when they are engaging in targeted attacks. This means that if you think you’re being phished, you should slow down and look for flaws. A “flaw” can be anything from a grammatically incorrect sentence to a purportedly official image or logo that doesn’t look quite right: No technical analysis required.
Most importantly, it’s crucial to remember that most legitimate businesses will not send you unsolicited emails with links to amazing offers or requests for your information. If they are, it’s probably time to consider using someone else – even if they are offering you four rolls of ember cloth, a stack of food, and 150 gold ;)
Have a Great (Phish-Free) Day!
Emsisoft Endpoint Protection: Award-Winning Security Made Simple
Experience effortless next-gen technology. Start Free Trial