Dorifel crypto malware paralyzes Dutch companies and public sector
Systems in the Netherlands are currently being hit hard by a new wave of crypto malware named “Trojan-Ransom.Win32.Dorifel”. Based on press reports as well as our own telemetry gathered through our Emsisoft Anti-Malware Network thousands of Dutch systems are already infected. The majority of them located in government, public sector or company networks.
Based on preliminary research “Dorifel” usually enters new networks and systems through the use of a different malware: “Citadel”. “Citadel” belongs to the family of financial malware and is closely related to the “Zeus” bot family. It comes to no surprise that this isn’t the first time that the “Citadel” bot net is used to infect systems with different malware. Just a few weeks ago at the beginning of July “Citadel” was used to infect tens of thousands of PCs with the “Reveton” ransomware.
Once “Dorifel” enters a new system it will copy itself into the user’s application data directory using a randomly generated sub-directory and file name. It then creates a short cut in the same directory it copied itself into that points to the malware file and starts it with the “-launcher” parameter. This shortcut is then added to the “Load” value in “HKCUSoftwareMicrosoftWindows NTCurrentVersionWindows” which causes the short cut to be executed on every Windows boot automatically.
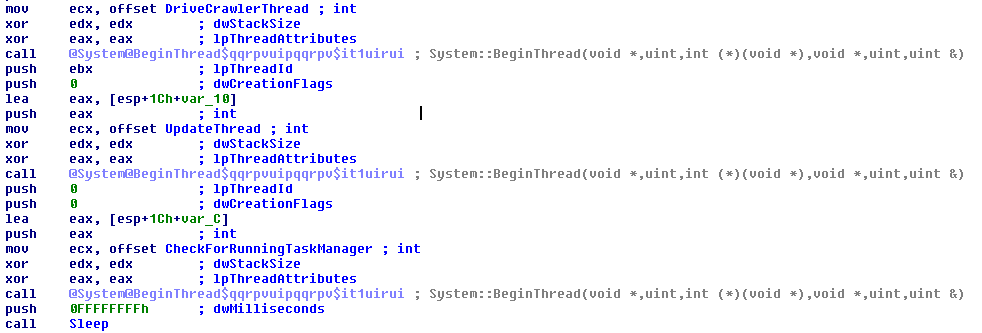
As soon as “Dorifel” is executed that way it will start three new background threads:
- The first thread is responsible for finding and infecting new Word and Excel documents. It is triggered once every 5 seconds and is explained in more detail in the next paragraph.
- The second thread becomes active every 1,500 seconds and contacts the malware’s command and control server located at hxxp://reslove-dns.com/bl/in.php. At this point the command and control server does not return any commands. It is to be expected that at one point in the future the command and control server will turn active and instruct “Dorifel” to download and install additional malware though.
- The third and last thread will poll the list of active processes once every 300 milliseconds. If a process with the image name “taskmgr.exe” is found running the malware immediately terminates. This is most likely a countermeasure to prevent detection by an Administrator looking at the running processes list.
The drive crawler thread
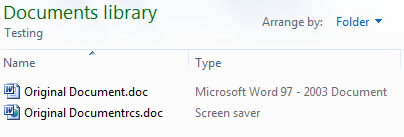
On the first look the second file seems legit as it has the expected .doc extension. A closer look though reveals that this file is of type “screen saver” and is therefore executable. The reason for this display is the unicode RTLO character that switches the display from left to right to right to left.
Once every 5 seconds the drive crawler thread becomes active. Its purpose is to look for Excel and Word documents on all drives and mapped network shares connected to the system that do not contain a “System Volume Information” directory. Once such a document is found “Dorifel” will infect it following these steps:
- The malware reads itself as well as the content of the document it wants to infect into temporary buffers.
- The document buffer is then encrypted using the RC4 encryption algorithm.
- A special marker (“[+++scarface+++]”) is added to the end of the malware file content buffer. This marker is used as a delimiter by the malware to later determine where the malware file ends and the encrypted document starts.
- The encrypted document is appended after the delimiter.
- The malware then generates a new file name based on the document name. It contains of the document’s base name without the file extension, followed by the unicode RTLO character (right-to-left overide, it essentially causes the following characters to be displayed backwards), the document’s file extension backwards and the .scr extension.
- The buffer containing the malware, the marker and the encrypted document is then saved to a new file with the previously generated file name.
- Last but not least the original document is deleted.
Once a document is infected that way it will show up almost as usual within the Windows Explorer and all standard Windows dialogs, but as soon as a user double clicks such an infected file it will not immediately open the document, but will run the malware instead. The malware then infects the system if not already infected and extracts and decrypts the content of the appended document to a temporary location. The document is then opened using the application registered for this document type. So for the average user everything looks normal while in reality he may have just infected his system with the “Dorifel” malware.
Cleaning a “Dorifel” infection
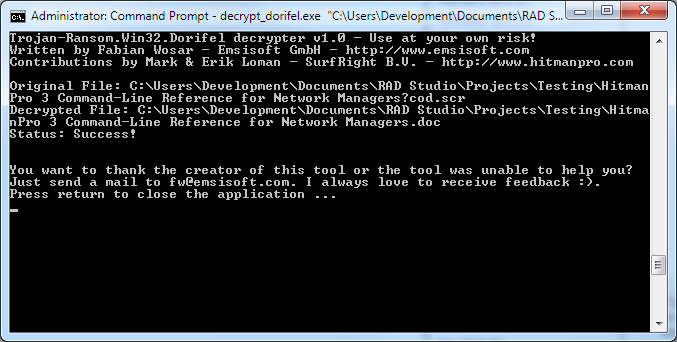
The Emsisoft “Dorifel” decrypter doing his work and decrypting documents encrypted by the “Dorifel” malware.
Due to the fact that “Dorifel” infects Word and Excel documents on the system as well as the network removal can be tricky. In order to remove “Dorifel” without loosing any documents we suggest the following:
Emsisoft Endpoint Protection: Award-Winning Security Made Simple
Experience effortless next-gen technology. Start Free Trial- Start the Windows Task Manager by right clicking the task bar and selecting “Start Task Manager”. This will trigger the self closing mechanism in “Dorifel” preventing “Dorifel” from interfering with the cleaning process.
- Download and unpack our “Dorifel” decryption tool to your Desktop.
- Run the “Dorifel” decryption tool. By default it will automatically scan your boot drive for any Dorifel infected documents and decrypt them. You can instruct the tool to scan specific folders, drives or network shares specifically by passing those as a parameter one at a time.
- Make sure the documents were decrypted correctly.
- Once you made sure that all documents were decrypted correctly you can remove all “Dorifel” infected files using Emsisoft Anti-Malware, the Emsisoft Emergency Kit or any other up-to-date anti-virus software.
- Since “Dorifel” was most likely installed on your system through “Citadel”, it is important that the “Citadel” infection is removed as well. Both Emsisoft Anti-Malware as well as the Emsisoft Emergency Kit detect and remove “Citadel” reliably.
If you have problems with these steps or find your system being reinfected over and over again you may want to contact our free malware removal support. The removal service is absolutely free even if you are not an Emsisoft customer yet.